Passwords and biometrics not testimonial compulsion under Article 20(3); smartphone searches must follow CrPC warrant safeguards (3)
HC held that an Investigating Officer may request an accused to provide password, passcode or biometrics, but a court cannot suo motu compel this, and any such search of a smartphone or email account must follow CrPC search and seizure provisions, ordinarily through a search warrant. Providing access credentials or biometrics does not amount to testimonial compulsion under Art. 20(3) and falls within the privacy exceptions recognised in Justice Puttaswamy, subject to strict safeguards and court control over disclosure. If an accused refuses despite warrant, the agency may attempt to technically access the device and draw adverse inference if data is lost. Applying these principles, HC set aside the trial court's orders compelling password disclosure and directing a polygraph test, noting lack of consent, and allowed the petition in part.
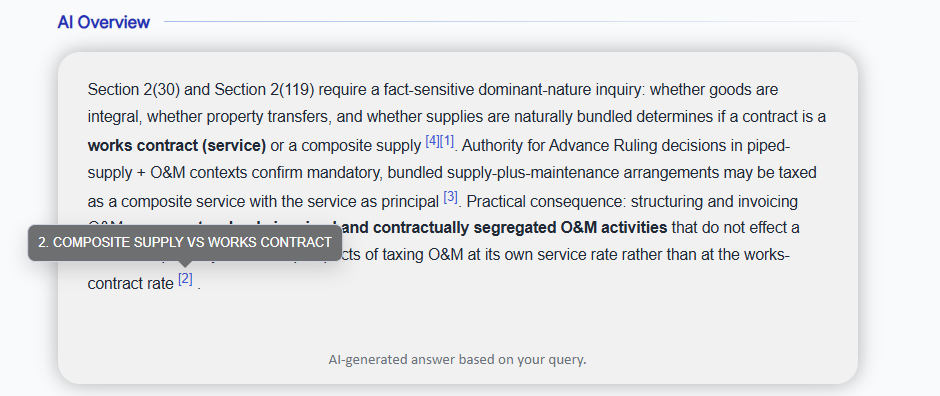
1. ISSUES PRESENTED AND CONSIDERED
1.1. Whether an accused can be directed to furnish password/passcode/biometrics for access to a smartphone and e-mail account, and whether the trial court's order dated 14.09.2020 directing the petitioner to "co-operate" by unlocking his devices was lawful.
1.2. Whether furnishing a password/passcode/biometrics for unlocking a smartphone or e-mail account amounts to "testimonial compulsion" or self-incrimination under Article 20(3) of the Constitution and Section 161(2) CrPC.
1.3. Whether directing access to data stored in a smartphone or e-mail account violates the right to privacy under Article 21, and what safeguards must govern search and seizure of electronic devices and data.
1.4. What procedural framework applies to search and seizure of smartphones, computers and e-mail accounts, including emergent searches, issuance of search warrants, and steps when an accused refuses to disclose password/passcode/biometrics.
1.5. Whether the trial court could order a polygraph test on the petitioner by order dated 23.09.2020 without prior notice and informed consent, and the effect of the bar on involuntary polygraph tests under Article 20(3) as interpreted by the Supreme Court.
1.6. Whether the trial court's refusal, by order dated 15.10.2020, to recall its earlier polygraph order was in accordance with law.
2. ISSUE-WISE DETAILED ANALYSIS
2.1. Direction to furnish password/passcode/biometrics and validity of the order dated 14.09.2020
Legal framework (as discussed)
2.1.1. The Court examined the scheme of the Code of Criminal Procedure, 1973 (Sections 91, 92, 93, 94, 100, 102, 165), and the Information Technology Act, 2000 (including Section 69(1)), as also the definitions of "document", "evidence" and "electronic record" under the Evidence Act and IT Act.
2.1.2. Chapter VII CrPC was treated as the governing framework for search and seizure, including of smartphones, computers and electronic data, subject to the safeguards prescribed therein.
Interpretation and reasoning
2.1.3. An investigating officer may, in the course of investigation, request or "direct" an accused or other person to furnish information or material, which can include a request to furnish password/passcode/biometrics to access a smartphone or e-mail account. Compliance is voluntary at that stage.
2.1.4. Accessing data on a locked smartphone or e-mail account is, in substance, a "search" of electronic equipment. It must therefore conform to the scheme for search and seizure under CrPC and, where applicable, the IT Act.
2.1.5. A court cannot, suo motu and without the search-and-seizure framework, compel an accused to furnish password/passcode/biometrics. The court is not part of the investigation and can act only on properly instituted applications, following statutory procedure and recording reasons.
2.1.6. A direction to "co-operate" with the investigation cannot be expanded into an automatic, enforceable compulsion to disclose password/passcode/biometrics, particularly when no search warrant has been sought or issued and no reasons have been recorded.
2.1.7. The Court treated the unlocking of a smartphone/e-mail account as analogous, for search purposes, to opening a locked premises under Section 100 CrPC: a person in charge may be required to facilitate access, but only in the context of a duly authorised search.
Conclusions
2.1.8. The order dated 14.09.2020, by which the trial court directed the petitioner to "co-operate" and provide password/passcode for his smartphone and e-mail accounts, was not based on the mandatory search-warrant framework, was unsupported by recorded reasons, and could not lawfully compel disclosure.
2.1.9. The order dated 14.09.2020 was therefore held to be not proper or legal and was set aside, with liberty to the prosecution to move appropriate applications and have them decided in accordance with the statutory scheme and the guidelines laid down by the Court.
2.2. Whether providing password/passcode/biometrics amounts to self-incrimination or testimonial compulsion
Legal framework (as discussed)
2.2.1. Article 20(3) of the Constitution and Section 161(2) CrPC were analysed in light of the Constitution Bench decision in State of Bombay v. Kathi Kalu Oghad, which distinguished "to be a witness" from mere furnishing of physical evidence such as fingerprints, handwriting samples and bodily impressions.
Interpretation and reasoning
2.2.2. Kathi Kalu Oghad holds that "to be a witness" means imparting knowledge of relevant facts by oral or written statements based on personal knowledge, and does not extend to mechanical processes such as giving fingerprints, handwriting samples or other physical identifiers.
2.2.3. The Court held that providing a password, passcode or biometrics functions in a manner analogous to providing fingerprints, handwriting, shoe-prints, or other identifying samples. It merely enables access to material (data/documents) that already exists; it is not, in itself, an oral or written assertion of fact.
2.2.4. The act of furnishing password/passcode/biometrics does not, by itself, incriminate the accused. The incriminating or exculpatory character lies, if at all, in the data obtained upon search, which must thereafter be proved at trial in accordance with the rules of evidence.
2.2.5. The data retrieved from a smartphone or e-mail account, even if incriminating, stands on the same footing as any other material object or document (e.g., a weapon, document, or other seized article). Its existence does not convert the facilitating act of unlocking into "testimonial compulsion".
2.2.6. Mere providing of password/passcode/biometrics does not constitute answering questions or "making a statement" within Section 161(2) CrPC. Hence, it cannot be equated with compelled testimony.
2.2.7. Acceptance of the petitioner's contention would effectively prevent collection of routine physical and electronic evidence (blood samples, DNA, handwriting, searches of premises, forensic access to computers and servers, investigation of cyber-crimes, etc.), which is contrary to established law.
Conclusions
2.2.8. Furnishing password/passcode/biometrics to enable access to a smartphone or e-mail account does not amount to "testimonial compulsion" or self-incrimination under Article 20(3) or Section 161(2) CrPC.
2.2.9. Directions, if otherwise legally permissible under the search-and-seizure framework, to provide password/passcode/biometrics do not, by that fact alone, infringe the right against self-incrimination.
2.3. Right to privacy and access to electronic data
Legal framework (as discussed)
2.3.1. The Court considered the recognition of the right to privacy as an intrinsic part of Article 21 in the decision declaring this right and the attendant three-part test of legality, legitimate state interest, and proportionality.
2.3.2. It also considered the nature of electronic data on smartphones and computers - including personal, financial, and sensitive information, and data stored on cloud services - and the reach of search powers under CrPC and Section 69 of the IT Act.
Interpretation and reasoning
2.3.3. A smartphone or computer is now a repository of extensive personal and professional data. Once access is given, an investigating officer typically acquires access to all data on the device and linked cloud services, which may include highly private and privileged communications.
2.3.4. Traditional concepts of "privileged" or "strictly private" documents cannot be directly transplanted to electronic devices, because the investigating officer, once into the device, sees all categories of data; perfect pre-segregation is not practically possible.
2.3.5. Nonetheless, legitimate investigation of crime falls within recognised exceptions to the right to privacy, provided there is legal authority, a legitimate aim (such as prevention and investigation of crime) and proportionality in scope and method.
2.3.6. Use of data obtained from devices for investigation does not, per se, violate the right to privacy if carried out within the statutory framework and for legitimate purposes. However, dissemination or public disclosure of such personal data is not automatically permitted.
2.3.7. The Court mandated that any disclosure or use of highly personal data in court proceedings must be regulated by a judicial order of the concerned court. No data accessed during investigation may be provided to third parties without written permission of the court seized of the matter.
2.3.8. Investigating officers bear a continuing duty to safeguard private information obtained from devices. Any unauthorised sharing or leakage would expose them to disciplinary or other legal consequences.
Conclusions
2.3.9. Properly authorised search and use of data from smartphones, computers and e-mail accounts for purposes of criminal investigation falls within the constitutional limits of the right to privacy under Article 21.
2.3.10. However, strict safeguards against unauthorised disclosure and misuse of personal data are required, and any wider use or publication of such data must be controlled by specific judicial orders.
2.4. Procedural framework and safeguards for search and seizure of electronic devices and data
Legal framework (as discussed)
2.4.1. The Court elaborated the application of CrPC provisions (Sections 91, 92, 93, 94, 100, 102, 165) to electronic devices and data, and Section 69(1) IT Act relating to compelled decryption.
Interpretation and reasoning
(a) Ordinary/regular course investigations
2.4.2. Where time permits, the investigating officer may issue a notice under Section 91 CrPC calling upon the accused or another person to produce the device or specified documents. Independently, or if such notice is not complied with, the officer may seek a search warrant under Section 93 CrPC.
2.4.3. A search warrant for a smartphone/computer/e-mail account must indicate: (a) the device/account to be searched; (b) its role in the alleged crime; (c) the nature and scope of the search; (d) place of search; and (e) an interdiction against disclosure of data obtained to third parties, to protect privacy.
2.4.4. Section 100 CrPC principles apply mutatis mutandis: a person in charge of a "closed place" must facilitate the search; by analogy, a device owner or custodian may be required to facilitate access once a valid warrant is issued.
(b) Emergent situations
2.4.5. In genuine emergencies (risk of imminent destruction of data or device, likelihood of loss of evidence), the investigating officer may, under Section 102 CrPC and Section 165 CrPC, seize and search devices without a prior warrant.
2.4.6. Such warrantless search and seizure is permissible only where there are reasonable grounds for immediate action. The officer must contemporaneously record in writing the grounds and the items sought, and forward copies to the Magistrate as required by Section 165.
2.4.7. Even if the search is procedurally defective, the admissibility of material seized is not automatically barred, but courts must be cautious in evaluating evidence gathered through an illegal search.
(c) Steps when accused refuses or obstructs access
2.4.8. If, despite a valid direction/warrant, the accused declines to provide password/passcode/biometrics, the prosecution may seek that an adverse inference be drawn, subject to the court being satisfied as to the nature and relevance of that inference.
2.4.9. Due to the risk that repeated incorrect passwords may lock or wipe devices, the accused should normally be given only one opportunity to provide the correct password/passcode/biometrics.
2.4.10. If the accused does not co-operate, the prosecution may request the court to direct the manufacturer or service provider (e.g., e-mail service provider, smartphone manufacturer) to unlock or provide access.
2.4.11. If the manufacturer/service provider cannot or will not provide access, the court may, on application, authorise the investigating officer to "hack" or otherwise technically break into the device or account, including by engaging specialised agencies.
2.4.12. If data is lost or destroyed during such technically authorised attempts, the prosecution may rely upon prior notice to the accused about possible adverse inference for non-cooperation.
2.4.13. Once access is obtained, the agency may: (a) clone the device or its hard disk and relevant cloud data; (b) block others' access by changing passwords; and (c) download and preserve relevant data for investigation and trial, subject to rules on electronic evidence.
(d) Minimum safeguards and handling protocols
2.4.14. The Court noted the absence of specific police rules for searching and preserving electronic evidence and set out minimum interim guidelines for computers, networked devices and mobile devices, including:
* association of a qualified forensic examiner in searches; * photographing equipment in situ and mapping connections; * not powering on devices that are off; * preserving volatile memory where devices are on; * isolating devices from networks (including via Faraday bags); * safely removing power sources and SIM cards; * seizing associated storage media and network hardware; * maintaining devices in a dust-free, temperature-controlled environment; and * full documentation and panchnama/mahazar of search, seizure and handling.
2.4.15. These guidelines are designed to preserve integrity of electronic evidence, prevent remote tampering, and ensure admissibility.
Conclusions
2.4.16. Searches of smartphones, computers and e-mail accounts must be rooted in CrPC provisions on search and seizure (and Section 69 IT Act where applicable), with duly recorded reasons, warrants where feasible, and strict procedural safeguards.
2.4.17. In cases of non-cooperation by the accused, courts may permit recourse to service providers or technical means (including hacking) and allow adverse inferences where justified, while still requiring the prosecution to prove the recovered data in accordance with evidence law.
2.5. Polygraph test: legality of order dated 23.09.2020 and recall order dated 15.10.2020
Legal framework (as discussed)
2.5.1. The Court relied extensively on the binding decision holding that involuntary administration of polygraph and certain other tests violates Article 20(3) and aspects of Article 21 (including the right to privacy and fair trial), and that such tests may be conducted only with informed consent.
Interpretation and reasoning
2.5.2. The trial court's order dated 23.09.2020 directing that the petitioner be subjected to a polygraph test was passed:
* initially on an oral request; * without a formal application being served on the petitioner or his counsel; * without hearing the petitioner; and * without obtaining his informed consent prior to passing the order.
2.5.3. The contention that the order merely "permitted" a polygraph test and that consent could be obtained later was rejected. The Court held that, in light of the Supreme Court's law, no order authorising administration of a polygraph test may be made without first obtaining informed written consent of the person concerned.
2.5.4. Silence or lack of express opposition by the accused cannot be construed as consent. Consent must be categorical, voluntary, and given after making the person aware of the nature of the test, its implications, and potential evidentiary effects.
2.5.5. In the present case, the petitioner had explicitly opposed the polygraph test, invoked his rights under Article 20(3) and Article 21, and filed a recall application asserting non-consent.
2.5.6. Once the binding law clearly prohibited compulsory polygraph testing and required consent, the trial court, when seized of the recall application, was bound to apply that law and recall its earlier order.
Conclusions
2.5.7. No polygraph test can be ordered or administered on any person without his/her prior informed written consent. Any such test conducted in the absence of valid consent would be void and its results inadmissible.
2.5.8. The order dated 23.09.2020 directing administration of a polygraph test on the petitioner, having been made without notice and without obtaining his consent, violated the constitutional protection against self-incrimination and the law declared by the Supreme Court, and was therefore set aside.
2.5.9. The subsequent order dated 15.10.2020 refusing to recall the polygraph order, despite the clear legal position and the petitioner's explicit non-consent, was held to be unsustainable and does not survive once the main order is quashed.
2.6. Overall disposition
2.6.1. The petition was partly allowed.
2.6.2. The order dated 14.09.2020 directing the petitioner to "co-operate" by furnishing password/passcode/biometrics for his mobile phone and e-mail account was set aside, subject to liberty to the prosecution to seek appropriate reliefs under the proper legal framework.
2.6.3. The order dated 23.09.2020 directing the petitioner to undergo a polygraph test was set aside as contrary to Article 20(3) and the binding precedent on involuntary polygraph testing.
2.6.4. The order dated 15.10.2020 dismissing the recall application was held not to survive and was effectively rendered infructuous by the quashing of the polygraph order.
2.6.5. Directions were issued for circulation of the judgment to police authorities and criminal courts in the State so that the investigative and procedural guidelines laid down therein are adhered to.
 • Category-wise results to explore all relevant documents on TaxTMI
• Category-wise results to explore all relevant documents on TaxTMI
 Help Us Improve - by giving the rating with each AI Result:
Help Us Improve - by giving the rating with each AI Result:
 TaxTMI
TaxTMI  TaxTMI
TaxTMI