Issued updated Security Manual for Licensed Defence Industries (SMLDI), 2025
X X X X Extracts X X X X
X X X X Extracts X X X X
....¤¯à¤®à¥‡à¤µ जयते Government of India Ministry of Defence Department of Defence Production SECURITY MANUAL FOR LICENSED DEFENCE INDUSTRIES (SMLDI) (Revised in June, 2025) 0 INDEX S. No.TopicPage No. 1List of Abbreviations used7 2Foreword9 3Executive Summary10 Category-A12 4Chapter 1- General Provisions, Requirements and Responsibilities13 1.1 Scope 1.2 Authority 1.3 Responsibility of the Management and Employees 5Chapter 2- Security Organisation and Personnel Security15 2.1 Company Chief Security Officer (CCSO) 2.2 Cyber Information Security Officer (CISO) 2.3 Security Staff 2.4 Responsibilities and duties of CCSO 2.5 Reporting procedure 2.6 Personnel Security 6Chapter 3- Security of Premises and Physical Security Measures22 3.1 General 3.2 Physical Security Measures 3.3 Layout of Premises 3.4 Reception Office and Visitors 3.5 Material Gate 3.6 Watch Tower 3.7 Setting up of Plant Security Council 3.8 Identity Badges, Entry Passes for personnel /vehicle and Parking of Vehicles 3.9 Keys of the organization 3.10 Late sitting in Office 3.11 Photography 3.12 Carriage of weapons 3.13 Carriage of liquor 3.14 Security measures for Sensitive / Secure/ st....
X X X X Extracts X X X X
X X X X Extracts X X X X
....tween two countries 9.5Movement 13Chapter10- Visits and Meetings74 10.1Visit of foreign nationals 10.2Meetings 10.3Nomination of employees from ILDC to attend Classified Meetings 14Chapter11- Training77 11.1General 11.2Security briefing 11.3Training 11.4Refresher Training 11.5Security training of Vendors/Contractors and Casual Labourers 11.6Training of project work Trainees 11.7Training on Cyber Security 15Chapter12- Miscellaneous79 12.1General 12.2Publicity and Photography 12.3Trials / Demonstration 12.4Rejects and Salvage 12.5Disaster Management 12.6Internal Security Audit 12.7Action on Completion of Audit 12.8External Security Audit 12.9Penalty for Non-compliance of security guidelines by ILDC 12.10Alternate Power Source 12.11Investigations of compromising emanations 12.12Retention of Classified Documents Generated Under IR&D Efforts 12.13Classified Waste Management 12.14Waste Management 12.15Compliance Statement S. No.TopicPage No. Category-B84 16Chapter 1- General Provisions, Requirements and85 Responsibilities 1.1 Scope 1.2 Authority 1.3 Responsibility of the Management and Employees 17Chapter 2- Security Organization and Personnel Security87 3 2.1Company Chief Security O....
X X X X Extracts X X X X
X X X X Extracts X X X X
....rise Resource Planning (ERP) 7.5 Physical and software security 7.6 Acquisition of Computer hardware and software 7.7 Miscellaneous aspects 7.8 Guidelines for computer users or operators 7.9Instructions for use of Internet within classified area / zone 7.10 Cyber Posture Enhancement via integration with Defence CSOC 23Chapter 8 - Subcontracting142 8.1General 8.2 Terms and conditions related to classified information 8.3 Engagement of Consultants/Advisers 8.4 Audit Recommendations 24Chapter 9 - International Security143 9.1Imports of Equipment/ Materials 9.2 Warning to Consignees 9.3Handing and Taking Over 9.4NDA for transfer of classified information between two countries 9.5 Movement 25Chapter 10 - Visits and Meetings145 10.1 Visit of foreign nationals 10.2 Meetings 10.3 Nomination of employees from ILDC to attend Classified Meetings 5 26Chapter 11- Training148 11.1 General 11.2 Security Briefing 11.3 Training 11.4 Refresher Training 11.5 Security Training of Vendors/Contractors and Casual Labourers 11.6 Training of Project Work Trainees 11.7 Training on Cyber Security 27Chapter 12- Miscellaneous150 12.1 General 12.2 Publicity and Photography 12.3 Trials and Demonstration 12.4 R....
X X X X Extracts X X X X
X X X X Extracts X X X X
....or Authentication A.44MFOMulti Facility Organization A.45MHAMinistry of Home Affairs A.46MoDMinistry of Defence A.47NCIIPCNational Critical Information Infrastructure Protection Center A.48NSANational Security Authority A.49OEMOriginal Equipment Manufacturer A.50OSAOfficial Secrets Act A.51PCPersonal Computer A.52PDCAPlan Do Check Act A.53PIDSPerimeter Intrusion Detection System A.54PSARAPrivate Security Agencies (Regulations) Act, 2005 A.55QAQuality Assurance A.56RAXRural Automatic Exchange A.57RESTDRestricted A.58SIEMSecurity Incident and Event Management A.59SOARSecurity Orchestration Automation and Response A.60SPFSender Policy Framework A.61SSOSingle Sign On A.62STQCStandardization, Testing & Quality Certification A.63TOP SECTop Secret A.64UEBAUser and Entity Behaviour Analytics A.65VMCVerified Mark Certificates A.66WAFWeb Application Firewall A.67WANWide Area Network A.68WMICWindows Management Instrumentation Code 8 Foreword The first revision of Security Manual for licensed defence industries involved in the production of defence products is issued in pursuance of para 12 of the Press Note No.2(2002 series) issued by the Department for Promotion of Industry and Internal T....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ecrets Act, 1923. 4. Indian Licensed Defence Companies can also have additional security safeguards over and above those prescribed in this Manual, specific to their requirements as considered necessary. The Government (MoD, MHA and their respective agencies etc) may also prescribe additional safeguards, if required, in any particular case and such safeguards would also be required to be followed by the company. Any violation/ non-adherence to any such instructions would be liable for action under the relevant Acts/ Rules/ Guidelines. 5. The companies would be required to follow this Security Manual whenever they undertake the manufacturing of any Defence item for which they have been issued Industrial Licences. The security instructions relating to the category, to which the Defence product belongs, would be applicable in such case. 6. The Security Manual may be revised with necessary consultation as required. # Defence Industrial Licence(s) include Industrial Licence/Defence Licence /Manufacturing Licence as issued by DPIIT, DoC and MHA. 9 Executive Summary Introduction This Security Manual provides the security architecture that needs to be put in place by DPSUs and the ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....cing production of defence products that it shall comply with the provisions of the Security Manual. Simultaneously, the ILDC shall take steps to create the security mechanism and apparatus in its production/manufacturing facility(ies) fully meeting the security standards prescribed in this Security Manual in order to safeguard the security of the Government classified information shared with ILDC as well as materials and end products in all phases of production activity till the end products are finally delivered/handed over to the authorised agency. The Security Manual contains below mentioned chapters for each category - 10 I. General Provisions, Requirements and Responsibilities - Enshrines general responsibility and requirements by the ILDCs, explains authority of CCSO, CISO, management tier etc. II. Security Organization and Personnel Security - Prescribes role, responsibilities, reporting mechanism of CCSO, CISO, duties of management tier, procedure to be followed in the event of breach of security etc. III. Security of Premises and Physical Security Measures- Prescribes parameters to be followed while designing the Layout of Premises and various other guidelines. IV. ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....racting, licensing and grant process, bidding, negotiation, award, performance, and termination, or any product, assembly or component arising out of such classified information. 1.1.3 When an ILDC is executing a Govt Project, dealing with classified information, material, document, it will be the responsibility of CEO, who in consultation with CCSO will earmark the areas as classified/sensitive, depending upon the nature of work being carried out in such areas/zones. 1.2 Authority: 1.2.1 The implementation of the manual is the overall responsibility of the Chief Executive Officer (CEO) / Head of ILDCs. 1.2.2 Agencies of MHA and MoD are the designated agencies for inspecting and auditing ILDCs who require or will require access to, or will store classified information and materials covered by this Manual. 1.3 Responsibility of the Management and Employees: 1.3.1 It is the responsibility of the management and every employee of the company to safeguard the security of all classified information and materials for which the access has been granted in course of duties or which comes into possession in any other way. 1.3.2 It is the duty of each employee of the company to immediat....
X X X X Extracts X X X X
X X X X Extracts X X X X
....al security policies, Internal Audit, Training, Review and up-gradation of Security procedures, Up-gradation of Security Equipment etc., Liaison with other Departments / Organizations, Civil and Law Enforcement Authorities and Intelligence Agencies of Centre and State, etc. The CCSO may be assisted by additional staff based on requirement and size of the company and should report directly to CEO or Executive Head of the Company. 2.2 Cyber Information Security Officer (CISO): Each ILDC shall appoint/ nominate a Cyber Information Security Officer (CISO). The CISO will be positively vetted by agencies of Government through Nodal Office, DDP before hiring and after every 3 years. The function may be accomplished by one senior officer having necessary and sufficient knowledge on IT system of the organisation in addition to his/her job. In case of company with more than Rs 250 crore turnover, a dedicated CISO shall be appointed. The CISO will be responsible for framing and implementing a suitable Cyber Security policy, conduct of cyber security audit and cyber security training for the organization etc. He shall also be responsible for incident management, identification of the organiz....
X X X X Extracts X X X X
X X X X Extracts X X X X
....uses pertaining to Information Security are incorporated into contracts/ agreements/ MoUs with service providers. iv. Ensuring that Incidents, especially repeat incidents are investigated and corrective action taken as identified through a comprehensive Root Cause Analysis (RCA). V. Implementing automated and continuous monitoring of security incidents and breaches, and maintaining record of the same. 2.2.1.3 Duties of Information Security Officer (At Wing / Division / Section level) The ISO shall be responsible for the following: - a) Training & awareness at Division/ Section level. b) Information privacy at Division/ Section level. c) Implementation of Cyber Crisis Management plan at Division/ Section level. 16 d) Information security audit of IT systems and controls at Division/Section level. e) Ensure that every IT Asset under his/ her administrative control is assigned a custodian. f) Ensure that an IT inventory file is maintained for the respective Division which will define the details of the IT Asset along with the custodian/ user. g) Ensure that the changes in the ownership are logged in the IT Asset file. The format for collating the details of IT Assets. h) ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....area/zone/manufacturing facility where the work related to MoD Project is going on and ensures that necessary boards indicating such areas are displayed. c) To keep himself fully conversant with all security instructions and ensure that the security instructions are fully understood by all employees and are implemented or complied with, within their respective sections and offices. d) To be responsible for the proper conduct, discipline and performance of all the personnel in Security department. e) To be responsible and ensure that fire service section is fully equipped and personnel are well trained. He shall take prompt action whenever necessity arises. f) To be responsible for the duties of his subordinate staff and carry out any other lawful and reasonable orders issued to him by management. g To carry out periodic surprise checks and maintains a record of such checks. h) To submit report to the CEO/Head of the sub units/division of the company indicating lapses noticed by him as and when it occurs. i) To arrange regular programs to apprise the employees on security matters. j) To maintain constant liaison with law enforcing agencies and nodal offices in Ministries. k....
X X X X Extracts X X X X
X X X X Extracts X X X X
....nauthorized receipt of classified material. b) Any significant vulnerability identified in the equipment or material being manufactured. c) Inability to safeguard classified material. d) Report of loss or suspected compromise. 2.5.3 The ILDC shall forward to designated agency the reports as given below: - S. No.PeriodicityTitle of ReportReport to be rendered 1QuarterlyLoss /recovery/ unearthed Arms and Ammunition and Explosives - Annexure- VIIINodal Office, DDP 2Immediately & QuarterlyFire accidents & other incidents / accidents - Annexure-XII & Annexure-XIII 3QuarterlyVisits of foreign business visitors- 19 Annexure-X 4QuarterlyAction taken report on, MoD/MHA agencies' visit - Annexure-XI 5QuarterlyCyber Incidents- Annexure-XII & Annexure-XIIINodal Office, DDP Incident pertaining to theft, fire, espionage, loss of ammunition etc., will be reported to nearest Police Station and Nodal Office, DDP immediately on occurrence, over and above, the same will be reflected in quarterly report. 2.6 Personnel Security: 2.6.1 Every ILDC shall ensure that no security leakage occurs through any personnel due to any reason, including, but not limited to, the following: - a) For persona....
X X X X Extracts X X X X
X X X X Extracts X X X X
....at effect. 2.6.3 It is the duty of every employee to bring to the notice of CCSO if they notice any suspicious behaviour of employees dealing with classified information like late staying in the office, making copies of document, frequent unauthorized absence, drunkenness and living beyond means etc. 2.6.4 Unconscious leakage due to carelessness or egoism often occurs at all levels, and even senior officers are not immune from this fault. It is the duty of every superior officer to make note of any such faults if any of his subordinates and suitably caution the officer against such lapses. 21 CHAPTER - 3 - Security of Premises and Physical Security Measures 3.1 General: All Defence related installations automatically fall under category of 'Prohibited Place' under the Official Secrets Act, 1923. A display board to this effect shall be installed in trilingual at the main gate and around, also contemplating 'trespassers shall be prosecuted'. 3.2 Physical Security Measures: Physical security means security in the form of safeguarding the installation which would comprise of providing adequate safeguards against an intruder coming from outside to damage the installation. This i....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... Under Vehicle Scanning System (UVSS) to be used for inspecting under carriage of vehicles. 3.3.16 All vulnerable areas/places, perimeter wall, gates, parking area and building/structures should be adequately illuminated. 3.3.17 Sitting of electric poles should not facilitate scaling of perimeter wall / fence by intruder. 3.3.18 'Armed Morchas' shall be placed at all vital entry/exit points including Main gate and Material gate. 3.4 Reception Office and Visitors: 3.4.1 Entry of visitors to classified area/zone/office shall be regulated through the Reception Office. The reception shall ascertain the purpose of visit and obtain the concurrence from the officer to be visited. A visitor management system be put in place for issue of photo passes to all visitors. Entry of the visitor in the classified area/zone/office would be authorised by CEO/Head of ILDC for official purpose only. 3.4.2 No visitor would be allowed to carry laptops, pen drives, mobile phones and any kind of storage devices or Bluetooth devices inside the premises. Entry of such items could be allowed only to non-classified area for the purpose of meetings that too on specific permission of CEO/CCSO of the instal....
X X X X Extracts X X X X
X X X X Extracts X X X X
....tower from the ground should be at least 15' to 20' in order to provide a clear field of observation all around. (iii) Staircase: The stair case leading to the watch tower should be made in such way that the security personnel on duty do not find any difficulty in negotiating the same while carrying their weapons and other equipment. (iv) Sentry Post: The cubicle on the top of the watch tower should facilitate in the performance of watch duties of the sentry and also allow him to use his weapon effectively when the need arises: a) The walls should not be more than 4 feet. b) There should be protection from incoming harsh sunlight and rain. c) The size should permit the sentry adequate space for movement. d) In case windows are provided they should have wide angles for maximum observation. 24 e) Lighting inside the post should be avoided to prevent outsiders from keeping a watch on the movement of the sentry and also facilitate a clear and effective observation of the area during hours of darkness / poor visibility. (v) Vision Devices: Day and night vision devices may be provided to the sentries based on the criticality of the installation and the assessed threat perception....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... permanent employees working in the classified area/zone/office, the CCSO may also issue following Identity documents: - a) Temporary Photo Identity Card: To be issued to personnel of the company or organisation who are working in the classified area/zone/office on temporary basis or for a short duration. b) Visitor Pass: A list of officers who are authorised to receive visitors as per the Company rolls shall be available at reception. Passes would be issued using Visitor Management System by the reception/security office on production of a valid identity photo document by the visitor (like passport, services ID card, driver's license, PAN card, Voters I card). The pass should be returned by the visitor at the gate on completion of the visit and endorsement of time and signature by the officer visited upon is to be checked. Online system should be in place for min 1year retention and tracking of visitor details along with the photo for future analysis / investigations required if any. c) Labour Pass: Labour pass with photo would be issued by the office of CCSO for casual labourers who are working for a specific period/term. These passes should be issued to labourers whose charac....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... security lapses, if any, on the part of the occupants of the rooms after they leave the premises. 3.10 Late Sitting in Office: Staff may sit in their office in the classified rooms/areas/zones under supervision of an officer. In case any staff is required to work on Holidays, or beyond stipulated working hours, a letter authorising him to do so would be sent to the CCSO by the departmental head. However, work classified as TOP SECRET and SECRET can only be performed under the supervision of an Officer. The person so authorised shall also be responsible for drawing and submitting of the room keys. 3.11 Photography: Photography/Videography on ground or aerial (through drones/UAVs) wherein any work related projects/ manufacturing of MoD is being carried out will not be permitted without the approval of MoD. Warning sign boards to this effect shall also be displayed at the main gate as well as inside the premises at vantage points. The guidelines of Ministry of Civil Aviation on Drone/ Drone threats issued from time to time shall be strictly adhere to. 3.12 Carriage of Weapons: Carriage of weapons, other than by the staff of CCSO would be strictly prohibited inside the Classified Z....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... outsiders. Wherever possible no construction zone of 50 ft from compound wall may be maintained. 3.16 Emergency response/contingency plan: In the event of emergencies like accidents, terror attacks, strikes, etc. the following procedure is to be followed: a) Activation of control room with immediate intimation to police and local authorities and a team of other officers, disaster management mechanism to be activated for taking charge of the situation. b) Display of contact details along with telephone numbers of the higher officials. 28 c) Display of contact details of local police, special branch, hospitals, bomb disposal team and local authorities in conspicuous places within premises of ILDC besides at security control rooms. d) Emergency exits/ route plan to be identified. e) The above actions should be in accordance with the Disaster Management Plan as per the guidelines/instructions issued by the National Disaster Management Authority/State Disaster Management Authority. 29 CHAPTER - 4 - Material Security 4.1 Incoming and Outgoing Material: No railway car, truck or other vehicle conveying crates, boxes, machinery, repair parts, fuel or other material should be ad....
X X X X Extracts X X X X
X X X X Extracts X X X X
....uthority: The CEO/Head of the Organisation will authorise a limited number of Officers who will be authorised to sign the material gate passes. The specimen signatures of authorised officers signing the material gate pass will be made available at the security gates. 4.6 Gate Pass Specification: The concerned officer of the security department in charge of the guard room should take the following action: - (a) Verify the signature in gate pass with the specimen. (b) Check the materials as per the gate pass. (c) Affix security outward seal and attest his signatures on the gate pass. 4.7 Returnable Material Register: Control SL. Nos. Should be given to the gate passes for taking out returnable materials A 'RETURNABLE MATERIAL REGISTER' should be maintained by the officer in charge. Proper entries should be maintained giving the reference numbers of the gate pass, authority for sending out materials. 4.8 Material Sent Out Register: It is the responsibility of the department concerned to account for the materials sent out. Proper register should be maintained giving the reference number of the gate pass, authority for sending out materials. 4.9 Abnormal Delays: The material....
X X X X Extracts X X X X
X X X X Extracts X X X X
.....15 Material brought on cash purchase Basis: Certain materials are purchased on cash purchase basis. Once a gate entry is made for such materials the materials should also be taken out only on material gate pass. This is accounting for control purpose. 4.16 Repair hand tools: Hand tools by plumber, electricians and mechanics of transport department who attend to repair will be taken out after making proper entries in the register maintained at the guard room. 4.17 Use of ERP/IFS: A system to be evolved for recording & tracking of materials using ERP/ IFS. 4.18 Transportation of Explosive and Other Classified Materials: a) There shall be empanelment of only security vetted transporter/carriers and drivers verified through local police for transportation of classified material/sensitive goods. b) In order to avoid any sabotage en-route it should be ensured that the vehicles carrying explosives and classified materials are escorted by armed guards. c) Secrecy should be maintained about the transportation plans/date/route etc. 32 d) Constant communication should be maintained while transporting explosives and classified materials. e) It is the responsibility of the company ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ment: A clearly laid out Data Classification policy shall be put in place by ILDC. Absence of policy and its implementation shall be treated as a violation of this Manual. Documents and equipment shall be classified as follows: - a) TOP SECRET: "TOP SECRET" shall be applied to information and equipment, the unauthorized disclosure of which could be expected to cause exceptionally grave damage to the National Security or national Interest. This category is reserved for the nation's closest SECRETs and is to be used with great reserve. b) SECRET: "SECRET" shall be applied to information and equipment, the unauthorized disclosure of which could be expected to cause serious damage to the National Security or National Interests or cause serious embarrassment to the Government in its functioning. This classification should be used for highly important matters and is the highest classification normally used. c) CONFIDENTIAL: "CONFIDENTIAL" shall be applied to information and equipment, the unauthorized disclosure of which could be expected to cause damage to National Security or could be prejudicial to the National Interests or would embarrass the Government in its functioning. d) RES....
X X X X Extracts X X X X
X X X X Extracts X X X X
....vers containing TOP SECRET documents will be marked with a diagonal Red Cross of one cm in width thickness extending from corner to corner on both the front and back covers. (a) A separate record of all TOP SECRET case files will be maintained in a register of TOP SECRET documents and docketed by the authorized officer. He should also carefully monitor movement of such files. (b) Even part files, if opened in relation to any classified document, will have the same security classification and will also be properly docketed. 5.3.3 SECRET files covers should carry a red vertical line in the centre. 35 5.3.4 TOP SECRET, SECRET, CONFIDENTIAL OR RESTRICTED drawings or tracings are to be marked in such a manner that the marking will be reproduced along with the main text whenever copies are made there from. 5.3.5 TOP SECRET, SECRET OR CONFIDENTIAL maps and charts are to be marked under or near the scale. For marking by stamp, red endorsing ink pads are to be used. 5.3.6 TOP SECRET documents should, wherever feasible, be printed or written on coloured paper, so that they may be easily recognized. 5.3.7 Marking for ILDC Developed Information and Equipment: Any information or materia....
X X X X Extracts X X X X
X X X X Extracts X X X X
....d files and materials shall be carried out during these inspections. 5.5.3 During the checking or inspections, the officers shall recommend destruction of classified papers and materials, wherever required. 5.5.4 A separate Diary and Dispatch book shall be maintained for TOP SECRET and other classified correspondence. 5.5.5 While making cyclostyled copies of SECRET or CONFIDENTIAL documents, a register indicating the number of copies, their copy numbers and to whom issued, would be maintained. The copy shall be made in a controlled environment under supervision. 5.5.6 End of Day Security Checks a) ILDCs that store classified material shall establish a system of security checks at the close of each working day. b) ILDCs that operate multiple work shifts shall perform the security checks at the end of the last working shift. 5.6 Care and Custody of Classified Documents and Equipment /Responsibility of Holders: ILDC authorized to store classified documents and equipment shall establish and maintain a system to deter and detect unauthorized intrusion or removal of classified documents and equipment from their facility. Personnel who have a legitimate need to remove or transport....
X X X X Extracts X X X X
X X X X Extracts X X X X
....on responsible for the receptacle. c) Duplicate keys should be kept in a sealed packet which will be in the custody of a nominated officer. A yearly report regarding this should be sent to the CCSO. The Duplicate keys will not be drawn in normal circumstances and shall be with the approval of CCSO only. The keys can be drawn or deposited by an employee who has been authorised to do so by the head of department/officer in charge of the section or office. While authorising employees to draw the keys, it would be ensured that rotation system is followed and casual labourer is not detailed for opening and closing duties. In case of loss of keys, the matter shall be reported to the CCSO. Separate duplicate key registers shall be maintained for record. d) In case of loss of a key, the matter should be immediately reported to CCSO and concerned lock should be changed. Even if the key is recovered subsequently, it should be regarded as compromised and a fresh lock and key should be issued with proper record. e) Keys should, where possible, be passed from hand to hand only. Should it be necessary to transmit a key by post, it will be made up into a 38 package so that the contents canno....
X X X X Extracts X X X X
X X X X Extracts X X X X
....rds both by day and by night to prevent the entry of unauthorized persons. The officer in charge of such a section shall ensure that only authorized persons have legitimate access to his section. If a paper is brought by a person not authorized to enter the SECRET Section, arrangements should be made for such paper being taken into the section without the person concerned being allowed access to the room. 5.11 Duplicating Work: Offices or Branches or Sections using Xerox and Photostats Machines etc., shall keep a record of all classified duplicating work done in their respective offices. The supervision of duplicating work will be done in accordance with the following: - 39 (a) Whenever any TOP SECRET letters or documents are required to be photocopied or cyclostyled, it would be done under the personal supervision of the custodian of the TOP SECRET documents. (b) Xeroxing a classified document of Top-Secret nature should be facilitated through a requisition slip duly signed by a designated officer by the CEO/ Head of the Company, with proper record maintenance at Reprography section. Similarly, in case of Xeroxing confidential document, requisition slips shall be signed by a s....
X X X X Extracts X X X X
X X X X Extracts X X X X
....eceiver shall scrutinize such covers carefully to ensure that no undue time has been taken in receipt and shall clearly indicate the time of receipt in the register of the receipts. iii. In every case, where single envelope is used, the appropriate classification of the enclosed document will be marked on the envelope, except when Restricted documents are dispatched by civil post and they may be sent in single envelope. iv. Care will be taken to ensure that envelopes are not of poor quality and are not overloaded. If the documents to be included are likely to be too heavy for an envelope, they shall be made into a parcel, or the envelope will be tied with a string. Cloth-lined envelopes, if available, may be used. V. Classified material shall be handled with similar care and attention to record keeping. (b) Sealing of Envelopes i. Inner envelopes of TOP SECRET, SECRET and CONFIDENTIAL documents shall be wax sealed. Special Seals shall be used to seal TOP SECRET documents. ii. The closing and sealing of "TOP SECRET" inner covers will be done under the personal supervision of the officers. The inner cover of the top secret documents will be sealed only by top secret seal bearin....
X X X X Extracts X X X X
X X X X Extracts X X X X
....T in locked brief cases. In case, brief cases are not available, these may be carried in a single sealed envelope. The documents too bulky to be carried in a brief case may be carried in locked and sealed canvas bag or boxes by messengers accompanying the officers. vii. If employees (other than officers) are required to carry classified mail, it shall be carried in a locked box or bag, the operating key of which shall be with the originator and the duplicate with the addressee. In the event of more number of addressees, a special box with multiple keys will be used, one key of which shall be with the originator and the rest (one each) with individual addressees. Such keys will not be handed over to the person carrying the box. viii. All classified mail inside the Mail Box or Bag shall be kept in a sealed cover: While doing so, it will be ensured that classification of the letter is not mentioned on the outer cover. ix. Section / Unit Officers must ensure that no mail is left undelivered with the person carrying them particularly on Fridays or on days preceding closed holidays. X. Similar care shall be taken in the movement of classified equipment. (d) Carrying Classified Docum....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ed Documents to Foreign Countries. Transmission of classified documents is prohibited in any form, either electronic/ fax or otherwise, to any foreign country. (g) Circulation and Carriage of Documents/Papers Containing Sensitive Information for Official Interdepartmental and Other Meetings. Utmost care will be taken to ensure security of classified information required to be circulated for Inter- departmental and Other Meetings. Following additional precautions will be taken :- i. Need to know principle will be strictly applied while circulating sensitive information. ii. No extra copies of papers etc. will be prepared. iii. Security classification commensurate with the contents will be assigned to the papers/documents required to be circulated. 43 iv. The papers/documents if required to be sent in advance will be sent by name and acknowledgement/receipt obtained. The document/ paper will be handed over to the addressee and not their personal staff. V. The paper/documents should be retrieved by concerned office after the meetings and accounted for. vi. Only authorized officers will carry such papers/documents for the meeting. These documents will not be carried to residenc....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... contract or as otherwise specified by the approving authority. 5.16.8 Non-disclosure agreement: Non-disclosure agreement may be put in place before sharing information with any outside agency. 5.17 Down Grading, Disposal and Destruction of Classified Documents and Equipment: 5.17.1 All organizations, departments, sections will carry out periodic destruction of documents (once in a year) to prevent their accumulation and consequent problems of accounting and security. Screening of documents for destruction should be done by a Board of Officers and the proceedings of such Board of should be approved by the Department Head prior to the destruction of the documents 5.17.2 Downgrading or Declassifying Classified Information. Information is downgraded or declassified based on the loss of sensitivity of the information due to the passage of time or on occurrence of a specific event. ILDCs downgrade or declassify information based on the guidance provided in a Contract Security Classification Specification or upon formal notification/ authorization. 5.17.2.1 An Officer will have no authority to downgrade / upgrade the security classification of a document received from other departme....
X X X X Extracts X X X X
X X X X Extracts X X X X
....sitive information /materials /documents should be retained permanently by the ILDCs. 46 CHAPTER - 6 - Communication Security 6.1 General: All communications are vulnerable to interception. Security of Communication is, therefore of paramount importance in an organization. 6.2 Telephones: 6.2.1 No form of telephonic conversation, including intercom PAX and hot lines, is secure. Every care has to be taken to prevent inadvertent leakage of classified information by discussing classified matters over the telephone. Following precautions shall be observed: - (a) TOP SECRET, SECRET and CONFIDENTIAL information should not be passed or discussed on telephone. (b) Before answering the phone or passing any official information on telephone, the person receiving the call should identify the caller beyond any reasonable doubt. In case of doubt, caller should be asked to give telephone no. and identity, which should be checked with the directory before calling back the caller. (c) The management should carry out periodical sensitisation w.r.t Social Media Usage, Cyber best practices and handling calls/manning Exchange. (d) Any attempt by the caller/ adversary to impersonate as govern....
X X X X Extracts X X X X
X X X X Extracts X X X X
....are in switched off mode and can be used to shoot and transmit still pictures or live videos. Therefore, cellular or mobile phones / Data Cards / Voice Modems including WLL phones are potent sources of breach of security of information. Also, no technology or device exists which can be fitted on them to make it interception proof. 6.3.2 GSM Monitoring system is a commercial off the shelf (COTS) equipment and is being manufactured by a large number of original equipment manufacturers (OEMs) across the world. Available equipment enables monitoring of Communication from briefcase sized equipment. A number of Indian vendors are marketing GSM monitoring systems. Due to their small size and portability, there is threat that inimical agencies may selectively employ such means/gadgets for interception of cellular communication from high density areas/ specific areas of activity. 6.3.3 The use of Cell phone shall be banned in areas/offices wherein classified work is in progress/documents are being worked upon. On special cases permission to carry mobile phones by critical staff, in these areas shall be recommended by the Head of department and granted by CCSO. Mobile phones are not permit....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ry out activities like development, implementation and evaluation of the facility IS program. To publish and promulgate IS security policy and procedures to address classified processing environment. 7.1.5 Threats to Computers security could emanate from internal sources such as subverted/disgruntled employees, as well from external sources such as the vendors of the Hardware/ Software, outsider maintenance staff or from intruders/hackers in the Cyber Space and hostile foreign countries /inimical agencies. Threats can manifest as Structured (automated methods of information gathering and attack - organised, determined and goal centric) or unstructured (network loitering, manual information gathering or attack and misuse by accident). Some of the Computer vulnerabilities that exist are as follows :- (a) Physical theft of Hard disks, Computer Storage Media, Keyboards with memory facility, used Printer Cartridges, Laptops etc. (b) Stealing /compromising data /information by remote access. (c) Susceptibility to Ransomware and Denial of Service Attacks (d) Susceptibility to Phishing, Smishing and Vishing Attacks (e) Accidental/Intentional cross connection between the Organization ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....here such systems may have an impact of the confidentiality, integrity or availability of systems / data. This policy must be made based on a realistic vulnerability / threat and risk assessment by qualified information security experts. The policy must have sign off from the senior most management of the organisation. If the organization also holds Critical Information Infrastructure, the Policy must be made in consultation with NCIIPC. The policy must cover all information devices and, inter alia, include Implementation of Security Controls as released by NCIIPC / CERT-In e.g. (a) Hardware / software inventory and controls 51 (b) Protection against malware (c) User and Password management including for all users handling critical / sensitive information including sub-contractors. (d) Revocation of privileges subsequent to termination of employees / contracts (e) Safe and verified backup and restoration mechanisms. These must be tested on a regular basis. (f) Configuration rules of Firewall, IDS/IPS, UTM, EDR/UEBA, SIEM/SOAR (g) Industry 4.0 policy for safety of Cyber Physical and SCADA/ICS Systems. (h) Disaster Recovery policy with focus on data security while assuring b....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... accountability should be clearly defined b) Require that each IS privilege / general user sign an acknowledgement of responsibility to adhere to Information security guidelines. c) Profiling of Information assets based on sensitivity of information by the Level of Concern for Confidentiality (C), System Availability (A) and Data integrity (I). The level of concern reflects the sensitivity of the information and the consequences of the loss of confidentiality, integrity or availability(CIA). Based on these matrices, need for protection levels and profiles in the form of security, audit, redundancy in the infrastructure, backup etc., shall be determined. d) Procedures should be defined about unique identification of user, user id removal on termination, transfer; change in roles etc., re-use of user id and user id revalidation for the use of any centralised IS resource. e) To maintain the CIA, control and audit logging mechanism along with monitoring system should be in place, for changes to data includes deterring, detecting and reporting of successful and unsuccessful attempts to change etc.Such monitoring system can be implemented by deploying solutions like Security incident....
X X X X Extracts X X X X
X X X X Extracts X X X X
....logies. These anti-phishing technologies encompass traditional methods such as Sender Policy Framework (SPF), Doman Keys Identified Mall (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC), alongside newer advancements like Authenticated Received Chain (ARC), Verified Mark Certificates (VMC), and Brand Indicators for Message Identification (BIMI) that collectively contribute to a comprehensive phishing prevention strategy. p) Develop and maintain a current baseline configuration of the system. Review and update the baseline configuration of the system periodically and when system components are installed and modified. q) In addition to above, some of the other guidelines which ILDCs need to follow are as follows - (I) Common Requirements: Types of cyber security incidents mandatorily to be reported to CERT- In: (i) Targeted scanning/ probing of critical networks/systems. (ii) Compromise of critical systems/ information. (iii) Unauthorised access of IT systems/ data 54 (iv) Defacement of website or intrusion into a website and unauthorised changes such as inserting malicious code, links to external websites etc. (v) Malicious code attacks su....
X X X X Extracts X X X X
X X X X Extracts X X X X
....physical and logical restrictions associated with changes to the system. (VI) Least functionality (i) Configure the system to provide only mission-essential capabilities. (ii) Prohibit or restrict use of the organisation-defined functions, ports, protocols, connections and services. (iii) Review the system periodically to identify unnecessary or non- secure functions, ports, protocol, connections and services. (iv) Disable or remove functions, port, protocols, connections and services that are unnecessary or non-secure. (VII) Incident Response Plan and Handling (i) Develop an incident response plan that provides the organisation with a roadmap for implementing its incident response capability Implement an incident-handling capability for incidents that is consistent with the incident response plan and includes preparation, detection and analysis, containment, eradication and recovery processes and procedures. (ii) (iii) Update the incident response plan to address system and organisational changes or problems encountered during plan implementation, execution or testing phases. (VIII) Incident Monitoring, Reporting and Response Assistance (i) Track and document system sec....
X X X X Extracts X X X X
X X X X Extracts X X X X
....plant functioning. Ownership of all processes and inventory held should be clearly defined with standby ownership. 7.5 Physical and Software Security: 57 7.5.1 Unless the physical security of a computer system is ensured, any attempt to protect its operations and data will be futile. Physical security and safeguard of hardware from damage, theft and unauthorized access and software and data from intentional, accidental or environmental corruption must be ensured at all costs. 7.5.2 Safeguarding the computer storage media, software, sensitive and proprietary data by :- (i) Safekeeping of computer storage media, (CDs, magnetic tapes, hard disk, USB drives etc). (ii) Shredding or secure disposal of console logs or printouts, used printer ribbons & carbons, damaged tapes and hard disks etc. (iii) Protection of Switches/Routers and other connectivity devices. 7.5.3 Network racks should be situated away from easily accessible public spaces like the pantry, cafeteria, restrooms, waiting rooms, hallways etc. Also these devices should be properly locked and must be under continuous surveillance using cameras. 7.5.4 Adequate protection is required both for the operating system softw....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... with physical access control systems/devices or guards. b) Maintain physical access audit logs for entry or exit points. c) Escort visitors and control visitor activity. d) Install secure keys, combinations and other physical access devices. 4. Access Control for Transmission and Output Devices. a) Control physical access to system distribution and transmission lines in organizational facilities. Control physical access to output devices to prevent unauthorized individual from obtaining access to controlled defence information. 5. Boundary Protection. a) Monitorand control communication at the external managed interfaces to the system and at key internal managed interfaces within the system. b) Implement subnet works for publicly accessible system components that are physically or logically separated from internal networks. c) Connect to external systems only through managed interfaces consisting of boundary protection devices arranged in accordance with organizational security architecture. 7.6 Acquisition of Computer hardware and Software: 7.6.1 Computer hardware, which is proposed to be procured, should be of an open system or architecture and the user should be free....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... PC. f) Where required CC EAL certification (Common Criteria-Evaluation Assurance Level) based on the protection profile required by the ILDC must be provided by the vendor. g) Certain windows feature like Power Shell Script, Windows Management Instrumentation (WMI) code (WMIC), process dumps can be exploited by a threat actor for malicious purpose. It is suggested that same must be disabled and may be enabled as and when need arises and disabled again. Behaviour based detection rules should be implemented for the same. 60 7.7 Miscellaneous Aspects: 7.7.1 Each ILDC shall formulate a clearly defined Cyber Security Policy, based on which a third party cyber security audit shall be conducted. This auditor shall be selected by the ILDC from the list of certified Cyber Security Auditors as published by Computer Emergency Response Team - India) CERT-In, on their web site. (i) The risk to secrecy of data due to the human factor should also not be underestimated. The following measures should be adopted in this regard :- a) Adequate separation of duties and restriction of access in every office so that no single person can individually compromise the entire system or data. b) Trien....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... in accordance with organisation-defined key establishment and management requirements. q) Cryptographic Protection Implement robust cryptography mechanism to protect the confidentiality of controlled defence information. r) Collaborative Computing Devices and Applications Prohibit remote activation of collaborative computing devices and applications. Provide and explicit indication of use to users physically present at the devices. s) Supply Chain Risk Management Plan Develop a plan for managing supply risks associated with the research, development, design, manufacturing, acquisition, delivery, integration, operations, maintenance and disposal of the system, system components or system devices which are related to or store or harness-controlled defence information. Review and update the supply chain risk management plan periodically. Protect the supply chain risk management plan for unauthorised disclosure. t) Acquisition Strategies, Tools and Methods. Develop and implement acquisition strategies, contract, tools and procurement methods to identify, protect against and mitigate supply chain risks. u) The Software must be developed and build in secure environments. Those e....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ermitted. Only in rare and exceptional cases, officers, for whom specific permission has been granted by CCSO, can use External / Portable Hard Drive within the classified zones/areas. External / Portable Hard Drives will be issued only to such individuals who possess the permission by name and it will be in their personal charge. Procurement of External / Portable Hard Drive will be done centrally by the CCSO with written approval of the CEO/Chairman/CMD, who may delegate the powers to the Unit Head for issuing written approvals. However, the responsibility and accountability of the same shall still rest with the CEO. All instructions relating to classified documents contained in this Manual are equally applicable to External / Portable Hard Drives. Carriage of External / Portable Hard Drive inside/outside the office premises is not permitted. Secondary storage Devices register will be maintained by the respective sections/departments. Internal physical check will be carried out within the concerned sections/departments every week and result indicated in 63 the register. Sections/departments will render a quarterly certificate to the CCSO regarding safe custody of the pen drive....
X X X X Extracts X X X X
X X X X Extracts X X X X
....difications etc. 7.7.5 Scanners: All scanners will remain in the physical custody of their owners and record of classified documents scanned should be kept. 7.7.6 Beacon and Siren must be integrated with the cameras used in Perimeter Intrusion Detection System (PIDS) as any camera can be tampered for 64 accessing in to the air-gapped camera network and can be used as pivoting point for further compromise. 7.7.7 Destruction and Weeding : a) Damaged and unusable Cartridge Tapes/ CDs/ DVDs/ Pen Drives and other CSM should be broken and destroyed by burning or as applicable to the weeding out paper based files and an entry to this effect be made in the register. CCTV recordings should be password protected. b) Bad / condemned hard disk should not be released even after it has been replaced by a new one. Such hard disks will be destroyed by following procedures as applicable to weeding out of classified files. c) Destructions should be carried out by application of corrosive Chemicals (acid or abrasive substances, emery wheel or disk sander) to the recording surface, and by shredding, incineration, disintegration, pulverization and smelting etc. 7.7.8 Cyber Security Audit: a) ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....d voice recognition, depending upon the nature of sensitivity of the data. User password is the most important aspect whose Confidentiality must be zealously guarded. Further, a password should have the characteristics laid down in this chapter. (vi) Audit trails are activated for keeping electronic record on the system regarding use of computer system by various users. Activities of a user be logged and appropriate audit trails be maintained on the system in electronic form. (vii) Before deleting the sensitive files, overwrite the files with some junk data to prevent restoration of the sensitive data by any means. Keep the backup of operating system software and application software under safe custody. One backup copy should be kept in different location as a precaution against fire hazards. (viii) Backup data should be periodically updated. Keep the software maintenance tool in your own custody. The periodic checking of backup inventory and testing of the ability to restore information validates that the overall backup process is working. This may be given to the engineer called to attend to the faults in the system as and when required. (ix) External CD writers will be under....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... must be enforced to mitigate the risk of data exfiltration. (xxix) Disable system accounts when - a) The accounts have expired b) The accounts have been inactive for an organisation - defined time period c) The accounts are no longer associated with a user or individual d) The accounts are in violation of organisational policy. e) Significant risks associated with individuals are discovered. (xxx) Notify organisational personnel or roles when - a) Accounts are no longer required. b) Users are terminated or transferred c) System usage or need to know changes for an individual (xxxi) Information in Shared System Resources. Prevented unauthorised and unintended information transfer via shared system resources. (b)DON'Ts. (i) Don't let any unauthorized persons use your computer system. (ii) Don't share your password with anyone, not even your colleagues. 67 (iii) Don't reveal the root password to any unauthorized person, particularly an outsider. (iv) Don't connect the computer directly to the mains. Also, no heavy electric load drawing machines like plain paper copier, shredding machines, coolers etc. should be connected to the source of constant voltage supply to th....
X X X X Extracts X X X X
X X X X Extracts X X X X
....SO. Internet connectivity should be provided to the offices only on a stand-alone PC. The Internet PC should 68 not be used for office work. The Internet PC will have its own peripherals such as UPS, scanner, etc. which will not be shared with any other system under any circumstances. PC will be kept isolated from all other systems, especially LAN/Intranet. Connection of any other system with Internet line for any purpose, whatsoever, is strictly prohibited. No official or personal files will be stored on the hard disk of Internet PC. Personal media will never be used on Internet PC. No sensitive/ classified office work will be done in Internet computers. 7.9.1 All official work will be carried out on a system belonging to Air Gapped Network. Air Gapped Network will be isolated from the Internet at the physical layer. The air-gapped network's devices should meet following criteria: (i) Must have a separate networking equipment, including switches and routers, accompanied by cables of a different colour to easily differentiate them from internet-related cables. (ii) Specially designated desktop computer (referred as Entry-Exit system) must be used for moving data into/out of Ai....
X X X X Extracts X X X X
X X X X Extracts X X X X
....joint partners (contractors /sub-contractors). (v) If the joint venture involves collaboration of foreign firm(s) then, connectivity of their computers with contractor system needs to be examined from security angle. (vi) All employees should be barred from using private email addresses (like Gmail, hotmail, yahoo, rediffmail etc.) for any form of official communications and emails from suppliers/contractors through private emails addressees should be barred, as far as possible. However, the employees should be discouraged to use official email id for registering into various non-official platforms like banking, insurance etc. (vii) Social media usage policy should be defined and enforced on all employees. Unless specifically required for discharge of their duties, employees must be prohibited from accessing social media sites from their official systems. Employees should be discouraged from publishing information related to their work. (viii) Server room/network room should have biometric access control systems with CCTV coverage in place (ix) Enforce approved authorisations for controlling the flow of controlled defence information within the system and between connected sys....
X X X X Extracts X X X X
X X X X Extracts X X X X
....r verification of C&A of advisors /consultants. Engagement of consultants/advisers shall be subject to signing of NDA. 8.4 Audit Recommendations: The ILDC shall receive the recommendations made by Audit Teams. The ILDCs shall make note of recommendations and take action as warranted as soon as possible but in any case not later than the timeline. 71 CHAPTER - 9 - International Security 9.1 Imports of Equipment/ Materials: (i) Where Sensitive Equipment/ Materials is bought or otherwise acquired by the ILDC, it should be ensured the equipment is securely packed and sealed and transported. The packages will not have any markings to indicate that the Equipment is Top secret / Secret. (ii) Top Secret and Secret Equipment/ Materials will not be shipped in Vessels / Flights which unload cargo in other countries or call at ports of unfriendly countries en-route. (iii) Bills of lading or other documents will not indicate the classification of the Equipment. Separate bills of lading may be made out for small consignments which are delivered to the Master of the Ship for personal custody during transit. These documents will indicate the equipment in general terms, e.g. Instrument, PCB....
X X X X Extracts X X X X
X X X X Extracts X X X X
....d equipment will ensure that they are fully aware of its classification and security measures to be adopted. Warnings as to the security measures necessary will be issued in writing. Top Secret and Secret Equipment will be Handed/ Taken over under the direct supervision of authorized senior officer only. 9.4 NDA for transfer of classified information between two countries: The names of the Government Authority of each of the two countries empowered to authorise the release and to co-ordinate the safeguarding of Classified Information related to the Contract and the channels to be used for the transfer of the Classified Information between the Participants National Security Authority (NSA)/ Designated Security Authority (DSA)/ Competent Security Authority (CSA) and/or Contractors involved shall be governed by non-disclosure agreement. 9.5 Movement: (i) Consignors of Top Secret and Secret Equipment will warn the consignee of the dispatch of equipment so that the latter is in a position to make adequate security arrangements to receive it. All such equipment will be suitably shrouded and accompanied by an escort to ensure that no unauthorized person gains an access to them surrept....
X X X X Extracts X X X X
X X X X Extracts X X X X
....f Foreigners visiting the Company. a) The Head of the Department / Division / Factory Office as the case may, will initiate the case for visit of foreigners, well in advance, giving the following particulars: - i. Full name of the visitor. ii. Nationality of the visitor. iii. Date of birth. iv. Parentage of the visitor. V. Permanent and Present address of the visitor. vi. Passport No with date and place of issue. vii. Validity of Passport. 74 viii. Visa details (types, data & place of issue and duration of visa) ix. Occupation and Name of the Firm / organization which the visitor is representing. X. Specific purpose of the visit. xi. If the foreigner has visited the establishment earlier, full details of the same is to be furnished. xii. Details of escort being provided for conducting the tour of the Foreign National(s). xiii. Address of Hotel/accommodation where the foreign visitor staying in India during the visit. xiv. The address of the Indian company with which the foreigner is having partnership/alliance etc. XV. Date & Time of visit xvi. Area to be visited xvii. Certificate that no classified document shall be shared with the foreign visitors. b) The part....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ibility of the CEO to ensure that classified information is not leaked. 10.3 Nomination of employees from ILDC to attend Classified Meetings: The CEO may authorize its nominated employee(s) to attend certain classified meetings pertaining to classified information / sensitive information. It is the responsibility of CEO for non-leakage of information. 76 CHAPTER - 11 - Training 11.1 General: It shall be the responsibility of the ILDC to provide all employees with security training and briefing, commensurate with their roles and responsibilities while dealing with classified information. Towards this, the ILDC may obtain defensive security, threat awareness and other educational and training information from the nominated agency of Government of India, Ministry of Defence. 11.2 Security Briefing: All employees should be briefed on security do's/don'ts on joining as a part of induction programme.The induction programme must include Cyber Awareness Capsule. Prior to being granted access to classified information, an employee shall receive an initial security briefing that includes the following: a. A threat awareness briefing. b. A defensive security briefing. c. An overvi....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ation and submission of the same to the respective College / University. 11.7 Training on Cyber Security: IT Division shall ensure that all personnel be appropriately trained on the Organization's Information Security policies commensurate with their roles and responsibilities and be kept up-to-date on any additions or changes to the policies. 78 CHAPTER - 12 - Miscellaneous 12.1 General: MoD will be the nodal agency for preparation, review and implementation of the manual. However, conducting inspection and audit would be the responsibility of MHA /MoD.MHA &MoD may take the assistance of other organizations like Agencies of MHA and MoD, DPSUs, NTRO etc. in the inspection or audit. 12.2 Publicity and Photography: No photography would be permitted inside the Classified Zone/Area pertaining to MoD projects without the approval of MoD. Photography, when permitted for official purposes, will be done under proper supervision and both the photos, soft copy of photograph and their negatives shall be appropriately classified. In the case of Top Secret and Secret Equipment, permission for photography or publicity will be granted by General Manager / Chief Executive of the manufactur....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ively. The disaster management plan should focus on data security while assuring business continuity. The BCP/DR backup sites (also referred as Secondary sites) should not be a source of data breach. Disaster Management Plan should be in line with the guidelines/instructions issued by the National Disaster Management Authority/State Disaster Management Authority. 12.6 Internal Security Audit: The ILDC shall carry out internal security audit to ensure verification of compliance of security instructions contained in this manual. The Security Audits are required to be conducted to ascertain the level of compliance of security instruction and procedures specified in the security manual. The audit shall be done at least on a yearly basis. If ILDC is Multi Facility Organisation (MFO), audit shall be done annually in each facility: - (a) Check compliance by all the establishments to realize the designed security objectives as enumerated in the security manual. (b) Verify the effective implementation of the instructions and identify lapses, if any. (c) Verify the efficacy of the existing Security & Fire Control System. (d) To check that adequate safeguards exist against espionage, s....
X X X X Extracts X X X X
X X X X Extracts X X X X
....session to the rightful owner or Ministry of Defence as the case may be, within 24 hours of such cancellation of the licence. 12.9.2 In case of breach, violation, non-adherence to the provisions of Security Manual, penal provision including financial penalties and denial of various RFPs/technical details/ToTs other contracts by the Government agencies including Service Headquarters, DRDO, DPSUs, etc may be imposed. 12.9.3 For an entity holding license under Arms Act, 1959 (Arms Act) strict adherence to the terms and conditions of the license is mandatory. Any violation of these terms and conditions may lead to cancellation of license and prosecution under the Arms Act, 1959. The provisions of the Explosive Substances Act, 1908 will also be applicable in cases involving in the manufacture, possession, storage or transport of explosives. 12.10 Alternate Power Source: An alternate power source is required to ensure that the system availability is maintained in the event of loss of primary power due to various reasons, including sabotage/subversion. 12.11 Investigations of compromising emanations: Compromising emanations are unintentional intelligence-bearing signals that, if int....
X X X X Extracts X X X X
X X X X Extracts X X X X
....sal. The guidelines must include explicit procedures for the destruction of electronic devices at the end of their life cycle, especially emphasizing the secure wiping of sensitive data from storage devices to prevent potential data breaches. 12.14.1 Waste Management from health perspective: - Classification of waste will be done as chemical, hazardous, toxic and recyclable collection, transport, processing or disposal, managing and monitoring of waste materials. The term usually relates to materials produced by industrial activity, and the process is generally undertaken to reduce their effect on health, the environment or aesthetics. Waste management is a distinct practice from resource recovery which focuses on delaying the rate of consumption of natural resources. All wastes materials, whether they are solid, liquid, gaseous or radioactive fall within the ambit of waste management. 82 12.14.2 E-Waste :- Once the electronic device reaches its end of its life cycle, the data on the device must be destroyed by techniques like erasing, wing, and degaussing. Storage devices such as hard disks and flash drives should undergo destruction, and the CISO must issue a destruction certi....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ng to the notice of his superior officer or the Company Chief Security Officer (CCSO), any breach of security regulations in general and/or in particular, any compromise on classified information or materials, either deliberately or inadvertently. 1.3.3 Every employee in the supervisory level is required to ensure, by frequent surprise checks, visits to office rooms and other places where his subordinates work or which they frequent and by all other means in his power, that the instructions laid down for the conduct of business and maintenance of security in company are fully understood and complied with by all of them. It will also be his duty to bring immediately to the notice of his superior officer, or to the officers responsible for security in his department, any instance of breach of security regulations by any member of the staff working under him or in that 85 department, or of any misconduct, of such a nature as would give rise to doubts about the staff member's integrity/ reliability from the security point of view. The CCSO will maintain the data of all such reported instances along with the Action Taken which will be made available to the external security audit tea....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ts and interaction with NCIIPC/CERT- In/Nodal Office, DDP and other agencies of MHA and MoD, as the case may be. The CISO must be of sufficient seniority to report directly to senior most management of the organization to ensure functional independence. The CISO may be assisted by additional staff as per the requirement of ILDC. It is the responsibility of the CISO to ensure that the organizational cyber security policy is adequately framed, implemented and audited to ensure necessary and sufficient protection from cyber threats. The CISO shall also clearly identify residual risk subsequent to implementation of requisite cyber security mechanisms. 2.2.1 Following organizational structure for Cyber Security shall be followed in ILDCs :- 2.2.1.1 Duties of Management Tier: The Management Tier, headed by the CEO/MD, assisted by CISO and CIOs, shall have the following roles and responsibilities :- 87 a) Responsible for taking executive decisions pertaining to ICT infrastructure for Organisation. b) Decision making body for overall policy matters. c) To take strategic decisions and evaluate opportunities in the field of Cyber Security and Cyber Defence, and countering cyber threat....
X X X X Extracts X X X X
X X X X Extracts X X X X
....not moved out of the respective division for which they were initially allocated without approval of the CISO. However, the same shall be properly documented. i) Ensure that the policies as laid down in this Cyber Security Policy are disseminated across to all personnel within the division. j) Ensure strict compliance with the laid down policies with respect to physical security of IT Assets. k) Comply with the instructions/ guidelines laid down as a part of the Cyber Security Policy. l) Act as the Nodal Officer for his/ her particular Wing/ Division/ Section as applicable for matters related to Cyber Security. 2.2.1.4 Duties of Cyber Security Division: a) Cyber Security Audits of the Organisation. b) Function as operations support and emergency response provider in case of Cyber Security incidents with the Organisation. c) Handling cyber threats, vulnerability detection/ mitigation etc. d) Advise IT division of the organisation for effective patch management of ICT infrastructure. Issue guidelines for timely dissemination of patches/Hot fixes/Service packs/Updates for IT assets. e) Formulate and disseminate Cyber Security advisory on latest cyber security threats and tre....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... security system for the premises under his charge, as required, over and above the security manual. l) To arrange Internal & External Security Audits m) To carry out a comprehensive personnel risk assessment, short listing of suspects and keeping them on watch list in coordination with HR and Vigilance Department. 2.4.1 When breach of security occurs, the main objectives shall be: - (a) To swiftly find out what has happened and modus operandi of the breach committed. (b) To minimise the damage done. (c) To investigate/ trace the culprit and report to CEO/ head of the company by fastest mode of communication. (d) To prevent recurrence and suggest remedial measures. (e) To report Cyber Attack/Data Breach to CISO. 2.4.2 If classified information or materials have been compromised/ lost/ found in wrong place, it is to be reported by concerned employee immediately in writing to the CCSO who shall take necessary action. 90 2.4.3 As and when cases of security violations are detected by the Security Staff, the same is to be reported to the CCSO on occurrence. These will be followed immediately by formal violation reports addressed to the head of the department who will thorough....
X X X X Extracts X X X X
X X X X Extracts X X X X
....liations. c) Carelessness in talk and in handling documents. d) In correspondence. e) In communication. f) Transmission of classified documents. g) Conversations. h) In case of any breach in the cyber security infrastructure of the ILDC, (National Critical Information Infrastructure Protection) NCIIP (Computer Emergency Response Team- India) CERT-In/ shall be notified at earliest with a copy to Nodal Office, DDP. The ILDC shall ensure that all requisite information / assistance is provided by its personnel to support activities of NCIIP / CERT-In/Nodal Office, DDP /other agencies of MHA and MoD. 2.6.2 To ensure that there is no leakage of information it is necessary to observe the precautions given below: - a) Character and antecedent verification through police, reference checks, previous employment verification has to be carried out for all persons before joining the ILDC b) In case any adverse police report is received against an individual dealing with classified matters, on re-verification, generally after every three years, he or she shall be transferred out immediately. Persons employed on TOP SECRET work shall be subjected to prior positive vetting by Nodal Office,....
X X X X Extracts X X X X
X X X X Extracts X X X X
....r walls, gates, lighting, access control system of entry, protection of vital stores and designating restricted areas. 3.3 Layout of Premises: The installation must have perimeter as under 3.3.1 A 8 Ft wall with barbed wire fence / concertina coil. 3.3.2 Spot lights with Day & Night CCTV Cameras. 3.3.3 There should be lighting arrangement all along the perimeter wall to allow clear observation during hours of darkness. 3.3.4 To reinforce manual observation and to have data available for investigation, the perimeter should be covered by CCTV with recording facility for 90 days. The Guidelines issued by Ministry of Electronics and Information Technology (MeitY) on CCTVs from time to time shall be strictly adhere to. 3.3.5 There should be minimum number of gates. The material gate should be different from those meant for the employees. 3.3.6 Biometric Access Control system must be installed. 3.3.7 At the employee's gate, there should be provision for Door Frame Metal Detector, Hand Held Metal Detector, and separate frisking room for ladies. 3.3.8 The gates must be covered by CCTV. 3.3.9 A control room to monitor the CCTV's be established and manned round the clock. 3.3.10 ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....e factory main gate. 3.4.8 Medics: First Aid Room & Tie up with local Hospitals. 3.5 Material Gate: Entry & exit of all material, raw, processes, garbage and scrap must take place only through the designated gate, which, as far as possible, should be divested from the employees. Provision of Weigh Bridge be made at the material gate 3.5.1 Communication: Gates are required to be connected to the security control room besides the office and residence of the security officer through a communication network that is dependable and operational around the clock. 95 Also, alternate means of communication in the form of radio telephony should be available at the gates/ watch towers to ensure uninterrupted communication. 3.6 Watch Tower: The following points need to be kept in mind while sitting and constructing watch towers, if required based on critically of the installation and the assessed threat perception: i) Sitting: Watch towers should be sited tactically so that the area around is dominated with clear visibility towards both the adjacent towers. There should be no dead ground or blind spots between any two towers. In case of any dead ground, the area should be covered with ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....egulated on the basis of photo Identity cards issued by the CCSO. The Identity Badge should have following details: a) Company logo b) Name and photograph of the employee c) Staff Number and pass number d) Signature of issuing authority e) Blood group f) Date of issue and validity g) Signature of employee h) Address of Unit 3.8.1 These ID cards are to be returned to CCSO on the date of expiry of their validity or when no longer required. The identity badges should be reissued once in 5 years so that latest photo is reflected on the badge. The Security Department should keep relevant account of badges issued. All employees shall follow the following instructions: - a) Every person, irrespective of designation, rank and status will display his or her Identity Card or any other identity document issued by the CCSO for verification by the security personnel on duty at all times while inside classified area/zone/office. b) Impersonation of the authorised holder of identity card or its alteration, destruction or transfer to another person would be a punishable under relevant laws. c) In case any individual found within the classified area/zone/office is not able to produce hi....
X X X X Extracts X X X X
X X X X Extracts X X X X
....all maintain a list showing name, designation, identity card number, local resident address and permanent home address contact number of the employees working in area/zone/office handling classified information. 3.8.6 The ID card, vehicle sticker and any other documents issued to an employee would be withdrawn and submitted to the CCSO prior to dismissal, suspension or transfer of the employee. 3.9 Keys of the Organization: 3.9.1 Keys to the offices rooms/areas/zones holding classified information should be kept in a secured designated placed at the office of CCSO. The access to the secured designated place will be strictly limited. The keys can be drawn or deposited by an employee who has been authorised to do so by the head of department/officer in charge of the section or office. While authorising employees to draw the keys, it would be ensured that rotation system is followed and casual labourer is not detailed for opening and closing duties. In case of loss of keys, the matter shall be reported to the CCSO. Key registers shall be maintained for record. 98 3.9.2 Prior to submitting the keys, the nominated person shall ensure that all the windows are closed and window blind....
X X X X Extracts X X X X
X X X X Extracts X X X X
....rrying of Smart phones high-end mobileswith camerasand other features also to be banned. (e) Patrolling in and around the Vital Points including night patrolling by Guards and Dog squads if required shall be carried out. Night patrolling 99 should be mandatorily provisioned at staggered intervals covering the entire perimeter along with vital points. (f) CCTV surveillance must be provided at entry / exit of Vital Points and other sensitive locations inside the factory. Recording of all CCTV footage should be kept for 90 days. (g) A two key system may be used for stores holding sensitive hardware wherein two authorised persons, one from Security and the other from stores / user Department, may be detailed. (h) Suitable Fire-fighting and Emergency / Disaster management measures to be instituted. (i) Proper foolproof access control to be established. (j) ILDC should ensure that adequate fire-fighting mechanism is in place so as to ensure that no untoward incidents happen in the premises due to fire. 3.15 Building Security: It shall be ensured that the buildings are constructed at a distance from the compound wall so that there is no intrusion from outsiders. Wherever possibl....
X X X X Extracts X X X X
X X X X Extracts X X X X
....corded by the gate staff. The time and nature of materials sent out shall the gate staff showing that the item is brought back. The time of return however should be noted. A specimen signature book showing the signature of the officer authorized to sign passes should also be maintained. 4.4 Material Gate Pass: A model material gate pass procedure is given below. The ILDC should, as far as possible, evolve a proper gate pass procedure to suit the conditions prevailing in the respective divisions and get it issued under the signature of the competent authority for compliance: - 4.4.1 Description of material gate pass: There will be two types of material gate passes, viz., (a) Non-returnable material gate pass; and (b) Returnable gate passes. 4.4.2 A non- returnable gate pass should be issued for the materials, which are taken out of the factory on permanent basis or for materials issued to sub-contractors etc. 101 4.4.3 A returnable gate pass will be issued for materials, which are sent out of the factory on returnable basis. Returnable gate pass will be issued only to such materials, which will come back in the same form without undergoing any change. For finished goods and....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... 4.12 Items brought by customers/suppliers as samples or for demonstration: Items brought by customers/suppliers as samples or for demonstration /tryout /rectification /repairs etc. should be allowed 'INWARD GATE PASS' by 'Security in-charge' at gates. The materials will be allowed to be taken out on the same gate pass after making proper entry in the office copy of the INWARD GATE PASS book. This procedure will be applicable to materials brought as samples. In case any electronic items(s) is/are brought inside by the customers or suppliers as samples or for demonstration/try out/rectification/repairs etc, it/they shall be authenticated through the CISO. 4.13 Bulk Materials: For bulk materials brought by contractors for their work, a proper gate pass should be issued for taking out the balance materials giving reference of the INWARD GATE PASS issued by the security department. 4.14 Secret Documents: The officers of the civil engineering department, purchase department and technical department should ensure that graded official documents of any nature including blue print should not be sent out without gate pass. A broad outline of instructions on handling of classified docum....
X X X X Extracts X X X X
X X X X Extracts X X X X
....the place of consignor and the place of consignees should to be informed. GPS tracking devices on the equipment / vehicles to continuously monitor the movement of classified materials / equipment may be installed. 104 CHAPTER - 5 - Handling of Documents and Equipment 5.1 Security Classification of Documents and Equipment: 5.1.1 Aims & objective of Document / equipment Security: To prevent a spy or an enemy agent from access to classified information/ equipment, to help CCSO in investigations into cases of leakage and spying and to implement the theory of security based on the principle of need to know, need to take and need to retain. Besides, classified document should be kept in such a secure place, where only authorized officials should have access. 5.1.2 Matters related to suspicious cases of leakages of classified information/theft should immediately be informed to CCSO and head of the company for a thorough investigation, taking serious view of such security lapses and breaches, dealing appropriately against delinquent official / person. However, outcome of investigations should be reported to CCSO and head of the company, for taking preventive and remedial measures for ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....orized to classify: The originator of the document will be authorized to classify the document / upgrade / downgrade the same. It is the responsibility of the originator that care is taken of such documents so that the same do not fall in the wrong hands. The overall responsibility of safeguarding classified documents will be of the CEO/ head of the company who shall take all necessary precautions / audits / review mechanisms as deemed fit. The level of officer in a company to initiate/handle classification of classified documents (Top Secret, Secret, Confidential & Restricted), should be designated by the CEO/Head of the Company. 5.3 Marking of Classified Documents and Equipment: The classified documents and equipment shall be prepared and marked as per the guidelines described below, as applicable, in the following manner: 5.3.1 All documents including Files, folders, binders, envelopes, and other items containing classified documents, noting of the file containing classified matter will have the security classification printed, stamped or typed in bold capital letters on the top and bottom centre of each page of the document. Any insertions, such as maps, or illustrations of ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....CCSO. d) Letters or documents including appendices, if any, shall have continuous page numbers. The total number of pages of a TOP SECRET or SECRET letter or document will be indicated in words below the security classification on the top centre of the front page. e) The Typist besides noting down his initials at the foot of each classified paper typed by him/her, should also note the number of copies made. f) Whenever a TOP SECRET document is required for preparation of additional copies for simultaneous examination, the same may be made after obtaining order in writing from the CEO/ Head of the ILDC. It is, however very essential that the originator be informed along with its distribution. 5.5 List of Documents, Checks and Annual Accounting: 5.5.1 All personnel who are holding classified documents and materials shall check all accountable classified documents and materials, and render certificate of safe custody on 31st December of each year to the next Superior officer. A copy of the certificate will be sent to the CCSO. 5.5.2 Two security inspections and verification shall be carried out, one by the Officer in charge of the section/wing/department/unit and another by the ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....iscussed / disclosed by him / her. 5.6.6 The holders of classified documents will carry out periodic checks. 108 5.6.7 Classified documents will not be studied in the presence of a person who is not entitled to see them or left exposed during the absence of the authorized holder. 5.6.8 When an individual is the sole occupant of a room and during working hours leaves the room for a short period/lunch hour, he must ensure that all TOP SECRET documents are locked in safes or cupboards. 5.6.9 The last two officials/late hour duty officers leaving the office will ensure that almirahs, drawer of tables containing classified documents inside the room / office are properly locked and that no document / paper has been left inside / on table, floor of the room and also in waste paper basket. They will deposit the sealed key to the Caretaker with proper entries. 5.6.10 No single official will open the almirah containing classified document in the office while joining the office in the morning. 5.6.11 The following instructions will always be strictly observed: - (a) When it is necessary to open a safe, it will be opened for the shortest possible time and locked immediately. (b) Keys,....
X X X X Extracts X X X X
X X X X Extracts X X X X
....as a classified document and should be kept in the custody of the officer. Classified work done on Laptops, PCs will not be stored in the hard disk or CDs and zip drives etc. If used, these will be handled as per the security classification of data contained therein. 5.8 Segregation and Care of SECRET Section: Any branch/ department or sections dealing with classified documents (i.e. Top Secret, Secret, Confidential and Restricted) must segregate its SECRET sections from the non-SECRET sections. There must be adequate provision of steel safes for the custody of classified documents in SECRET sections. Doors of rooms of these sections shall be provided with security locks of proper make and quality in addition to the existing inset locks. Non adherence to this Provision shall be viewed as violation and shall entail punitive action. 5.9 Security Arrangements for SECRET Section: The window or the skylight of the SECRET section should be fitted with wire netting or Iron bars and, if it is accessible from outside, it should, in addition, be fitted with strong wire meshing. Lighting arrangements both inside a section dealing with classified documents and in the corridors approaching it....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... his personal staff so authorised by him. The diarizing of SCERET documents may be entrusted to the lower level at the discretion of the concerned officer. The responsibility of the safe custody of the documents will, however, rest with the officer concerned (ii) The diarizing of CONFIDENTIAL documents may be carried out by selected nominated office staff. 5.14 Transmission of Classified Documents: (a)Preparation of Envelopes: (i) TOP SECRET, SECRET and CONFIDENTIAL documents will be sent in two envelopes. To assist the recipient in verifying that there has been no tampering in transit, the inner envelope will invariably be a new one. The outer envelope will bear only the address, and will not be marked with the security classification of the contents. The inner envelop will be marked with the appropriate security classification, and if TOP SECRET, it will also be marked "to be opened personally by or officer officiating" (the holder of an appointment or the name of the individual being stated). (ii) In respect of TOP SECRET and SECRET documents, the dispatcher shall sign the inner cover at two prominent places (e.g. joint-line or the flap), with his name, date and time of dis....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ents be carried loose in the hands of the messengers/ orderlies. (ii) A messenger carrying secret covers should not leave them unattended at any time till they are delivered. (iii) Within the Same Block or Building: TOP SECRET files or documents shall be taken only by the officer entrusted to deal with them. In rare cases, if a document is to be conveyed through another Officer authorized to handle the document, it shall be put in a single sealed envelope and then carried. SECRET files or documents shall be taken by hand by a person authorised 112 by CEO/ Head of ILDC. CONFIDENTIAL files or documents may be transmitted through any member of the staff entrusted to deal with it. (iv) Movement of Classified Documents Within the Same Station: Movement of TOP SECRET documents between one block to another within the station, shall be through an authorized courier and not through peons or registry. If the carriage involves movement in public area Journey shall be undertaken only in an authorized transport. Wherever feasible, a second person shall also be nominated to accompany the courier. (v) The responsibility of the safe custody and handling of the TOP SECRET document will be tha....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... secure place to which no outsider may have access. (iv) Whenever an officer requires a Top Secret document for meetings /discussions, etc. either at the place of his posting or at a place other than the place of posting and Top Secret documents have to be taken out of the office, the following procedure shall be followed: Only Officers authorized by CEO/ Head of the Company will be permitted in special circumstances for taking top secret documents out of the building to facilitate official meetings with explicit approval of CEO / Head of the Company. (e) Transmission of Classified Documents to Outstations within India: Classified documents will be dispatched through civil postal service subject to the under mentioned instructions :- (i) TOP SECRET. TOP SECRET documents will only be sent by special couriers. In no circumstances will they be transmitted by civil post. TOP SECRET mail, however, will not be dispatched by "AIR DESPATCH SERVICE." unless accompanied by special couriers. (ii) SECRET or CONFIDENTIAL. Documents can be sent by Registered Civil Post and marked "Registered AD" post on the outer envelope of documents. (iii) RESTRICTED. Document may be sent by civil post, ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....bcontract. Prior authorization shall be obtained by the ILDC in writing from the Government Agency having classification jurisdiction over the information involved for this purpose. 5.16.4 Disclosure between Parent and Subsidiaries: Disclosure of classified information between a parent and its subsidiaries, or between subsidiaries, shall be accomplished in the same manner as prescribed in 5.16.3 for subcontractors. 5.16.5 Disclosure in an MFO: Disclosure of classified information between facilities of the MFO shall be accomplished in the same manner as prescribed in 5.16.2 for employees. 5.16.6 Disclosure of Classified Information in Connection with Litigation: ILDCs shall not disclose classified information to a legal advisor or consultant or representative or any other person acting in a legal capacity unless the disclosure is specifically authorized by the agency that has jurisdiction over the information. ILDCs shall not disclose classified information to any court except on specific instructions of the agency which has jurisdiction over the information. 5.16.7 Disclosure to the Public: ILDCs shall not disclose classified or unclassified information pertaining to a classifi....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ied waste, indicating individual detailed for supervision and the time and place shall be maintained by the Sections, in order to pin point the responsibility in case of breach of security. b) In no circumstances shall waste paper, drafts, spoiled forms, used carbon papers, unnecessary duplicates, stencils, blotting paper, impression of official seals and stamps relating to or used in connection with classified document be allowed to fall into the hands of unauthorized persons. 116 5.17.7 Record Rooms Following instructions will be applicable for security of classified documents stored in the record rooms: - a Isolated room shall be used for storing classified documents and equipment. They will not be kept in the room where other non-classified documents are stored and kept. b) Proper fire-fighting arrangements will be made to deal with outbreak of fire, suitable fireproof cupboards shall be made use of for storage of TOP SECRET, SECRET and CONFIDENTIAL documents. c) Records/files/documents from Record Rooms will only be issued on a requisition, stating the purpose and duration for which the records are needed. The requisition should be signed by an officer. A record of the d....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... will not be used. (g) If it comes to notice that an intruder has come on the line and some information has come to the knowledge of the listener, the same should be brought to the notice of senior officers and CCSO so that remedial measures can be taken. 118 (h) A thorough physical check of the PABX phones or instruments or boxes should be made periodically by the office of CCSO to ensure that these are not tampered with. (i) All vulnerable points in the intercom system should be protected by wooden or metallic boxes with locking arrangement. (j) Telephone conversation is totally unsafe; thus, if at all classified information has to be passed on phone, proper secrecy device should be used. (k) All telephones should be provided with a caller ID facility. (l) Only authorized person be nominated for maintenance of PAX / outdoor plant, furthermore records of same be maintained. 6.3 Cell or Mobile Phones / Data Cards / Voice Modems: 6.3.1 Cellular or Mobile Phone / Data Cards / Voice Modems are highly insecure medium for communication purposes, since it works on UHF and VHF and is prone to interception by Frequency Modulation receivers. These gadgets can also be used as effect....
X X X X Extracts X X X X
X X X X Extracts X X X X
....n a register. The record will include the following details: - a) Time of Fax sent or received. b) Title of document. c) Number of pages d) Sent to or received from. e) Designation of Officers or office where Fax is sent. f) Officer authorized to dispatch the Fax. g) No "Top Secret" message should be transmitted on FAX. 120 CHAPTER - 7 - Computer and Cyber Security (Information Systems Security) 7.1 General: 7.1.1 Information systems (IS) that are used to capture, create, store, process or distribute classified information must be properly managed to protect against unauthorized disclosure of classified information, loss of data and integrity to ensure the availability of the data and system. 7.1.2 The organization must, at all times, be in strict compliance with the IT Act 2000, as amended in 2008 and as amended from time to time. 7.1.3 Protection requires a balanced approach in IS security features to include, but not limited to, administrative, operational, physical, computer, communications and personal controls. Protective measures commensurate with the classification of information, the threat and the operational requirement associated with environment of IS. 7.....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... for information security; (ii) Implementing and operating controls (administrative, technical and physical) to manage an organization's information security risks in the context of the organization's overall business risks; (iii) Monitoring and reviewing the performance and effectiveness of the ISMS; and (iv) Continual improvement based on objective measurement. 7.2.5 This International standard adopts the "Plan-Do-Check-Act" (PDCA) model, which is applied to structure all ISMS processes. PDCA provides a structured approach for organizations to achieve continual improvement. 7.2.6 Norms of ISO 27001 is the comprehensive evaluation of the technical and non- technical security features of an IS and other safeguards, made as part of and in support of the accreditation process, to establish the extent to which a particular design and implementation meet a specified set of security requirements. The compliance process subjects the system to appropriate verification that protection measures have been correctly implemented. The internal system shall review that all systems have the appropriate protection measures in place and validate that they provide the protection intended. 7.3 ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ystems by the following methods - (i) Initiating a device lock after organisation-defined period of inactivity (ii) Requiring the user to initiate a device lock before leaving the system unattended (iii) Retain the device lock until the user re-establishes access using established identification and authorisation procedures. (iv) Conceal, via the device lock, information previously visible on the display with publicly viewable image. 123 7.3.1 Having implemented adequate measures to secure their information infrastructure, the CISO should also ensure that compensating controls and residual risk are enumerated and sign off obtained from management. Review and Evaluation of Cyber Security Policy Cyber Security Policy of the Organisation shall be reviewed at least annually and updated in response to any changes that would affect the assumptions from the baseline risk assessment, such as significant security incidents, new vulnerabilities, new regulations or changes to the Organization's infrastructure. The review shall include an assessment of the policy's effectiveness based upon: - (a) The nature and number and impact of recorded security incidents. (b) Cost and impact o....
X X X X Extracts X X X X
X X X X Extracts X X X X
....d be in place to track, inventories, to carry out OS patches, IOS/Firmware updates and Configuration Management of information Systems. k) All Internet facing Web sites /Applications, necessary protections at Network Layer and Application, like security during transmission, Application Security and Database security should be in place by using appropriate security components / measures. In addition, all these public facing applications and portal should be protected using Content Delivery Network (CDN) and Web Application Firewall (WAF). Also Single Sign On (SSO) with Multi Factor Authentication (MFA) must be enforced on all portals. l) The Number of Internet Connections shall be controlled by CEO/ Head of Company as per the company policy. m) Centralised Anti-Virus management solution should be in place for effective implementation of Anti-Virus solution. n) System should be in place for internal incident management as well as for implementation of time to time necessary guidelines / measures from Computer Emergency Response Team - India (CERT-India)/ National Critical Information Infrastructure Protection Centre (NCIIPC); and should be able to detect any violations to existin....
X X X X Extracts X X X X
X X X X Extracts X X X X
....pplications related to Big Data, Blockchain, virtual assets, virtual asset exchanges, custodian wallets, Robotics, 3D and 4D Printing, additive manufacturing, Drones. (xx) Attacks or malicious/suspicious activities affecting systems/servers/software/ applications related to Artificial Intelligence and Machine Learning. (II) Configuration settings: (a) Establish document and implement the configuration settings for the system that reflect the most restrictive mode consistent with operational requirements. These configuration settings must be organisation-defined consistent with overarching requirement to protect, controlled defence information. (b) Identify document and approve any deviations from the establish configuration settings. Such deviations must be granted only as an exception after due deliberation be a collegiate. 126 (III) Configuration change control: (a) Define the type of changes to the system that are configuration- controlled. (b) Review proposed configuration-controlled changes to the system and approve or disapprove such changes with explicit consideration for security impacts. (c) Implement and document approved configuration-controlled changes to the s....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ination and Transfer a) When individual employment is terminated - (i) Disable system access within the shortest timeframe which is organisation-defined (ii) Terminate or revoke authenticators and credentials associated with the individual. (iii) Retrieve security-related system property from the terminated individual. b) When individual is reassigned or transferred to other positions in the organisations - (i) Review and confirm the ongoing operational need for current logical and physical access authorisation to the system and facility. (ii) Initiate information security-related transfer or reassignment actions within shortest timeframe that is organisation- defined. (iii) Modify access authorisation to correspond with any changes in operational need. 7.4 Enterprise Resource Planning (ERP): Enterprise Resource Planning (ERP) may be implemented as system integrates internal and external management information across the entire organization, tracking of all processes, materials and personnel in the plant. ERP systems automate this activity with an integrated software application. The purpose of ERP is to facilitate the flow of information between all business functions in....
X X X X Extracts X X X X
X X X X Extracts X X X X
....he user to initiate a device lock before leaving the system unattended. (b) Retain the device lock until the user re-establishes access using established identification and authorisation procedures. 129 (c) Conceal, via the device lock, information previously visible on the display with publicly viewable image. 7.5.7 Remote Access (a) Establish usage restrictions, configuration requirements, and connection requirements for each type of allowable remote system access. (b) Authorise each type of remote system access prior to establishing such connections. (c) Route remote access to the system through authorised and managed access control points. 7.5.8 Authorise remote execution of privileged commands and remote access to security-relevant information. 1. Monitoring Physical Access a) Monitor physical access to the location where the system resides to detect and respond to physical security incidents b) Review physical access logs periodically. 2. Alternative Work Site a) Determine alternate work sites allowed for use by employees. b) Employ adequate physical requirements at alternate work sites at par with those employed at main work site. 3. Physical Access Control a....
X X X X Extracts X X X X
X X X X Extracts X X X X
....urity point of view should be carried out. While awarding contract for maintenance it should be ensured that too many engineers from the maintenance company are not allowed to work on the systems. It should also be ensured that when the service engineer undertakes the maintenance or repair job, a knowledgeable representative of the user invariably remains present throughout and ensures that no data or information from the computer is downloaded and taken out by the service engineer. Positive vetting of the firms offering AMCs will be as per the guidelines and processes issued by the Government from time to time. 7.6.4 The outsider maintenance Engineer should not be allowed to install his own keyboards and other accessories as an interim measure till repaired part is returned, as his accessory may have data capturing tools like key logger. When his accessory is taken back, it may have valuable data captured from the computer. 7.6.5 While installing the operating System, only the utilities /components required by the user should be installed/ enabled. Some of the utilities listed below which are enabled by default with the bundled software must either be disabled or configured on n....
X X X X Extracts X X X X
X X X X Extracts X X X X
....tioners of cyber security applied to the principle ILDC must equally carry forward to all contractors / sub-contractors employed in the project and they may also sign non disclosure agreement. i) The passwords/credentials of various applications must never be stored on devices (like in browsers/test files etc). Also access credentials should never be pasted / written on advice. j) The IT Employees must be sensitized that sensitive information like IP Ranges; Passwords and Usernames etc must never be maintained in Personal Diaries. 132 k) Air-Gapped Systems should not be used for accessing Internet using Mobile Hotspots/USB Dongles. l) Information in Shared System Resources prevent unauthorised and unintended information transfer via shared system resources. m) Network communication - Deny by Default - Allow by Exception. Deny network communication traffic by default and allow network communication traffic by exception. n) Transmission and Storage Confidentiality Implement cryptographic mechanism to prevent the unauthorised disclosure of controlled defence information during transmission and while in storage. o) Network Disconnection Terminate network connections associated ....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... software developer must make all efforts to maintain trusted source code supply chain by employing automated tools or comparable processes to address the security of internal code and third party components and manage related vulnerabilities as available from time- to-time. Use of trusted software/hardware components in facility handling/developing sensitive technology is mandatory z) The software developer must maintain provenance for internal code and third party components incorporated into the software as Software Bill of Material (SBOM) and supply the same to BUYER at the time of delivery of the software as well as each software update. aa) The software developer must employ automated tools or comparable processes that check for security vulnerabilities. 7.7.2 Cataloguing of CDs/ External / Portable Hard Drive: The CDs (RW), Cartridge Tapes, External/Portable Hard Drives used should be serially numbered with name of the concerned written in indelible ink. A register should be maintained for taking it on charge and destroying those that become unserviceable, and periodical checks should be carried out. Supply of blank storage medium for use of the PC holders will be made on....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ts on the external system as specified in the organisation's security plans. (ii) Retention of approved system connection or processing agreements with the organisational entity hosting the external system. d) Restrict the use of organisation - Controlled portable storage devices by authorised individuals on external systems. 7.7.4 Laptops/Palmtop/Electronic Notebook: Carriage of Laptops/ Palmtops/ Electronic into or out of classified zone/area without permission from CCSO is not permitted. Following precautions should also be taken to ensure security of information: - (a) No personal Laptop/ Pen drive/ thumb drive/ hard disk/ palmtop/ Electronic Notebook and mobile phones with Blue tooth / Wireless Internet (4G/5G) should be permitted to be brought into the classified area/zone by the visitors or the employees. (b) In case a Laptop/Palmtop/Electronic notebook is required to be brought inside for a specific purpose, the Bluetooth/WI-FI feature, if present, should be disabled and the user/owner should be escorted till his exit to prevent any enabling during the visit. (c) Any laptop taken out for presentation should be checked for containing any unauthorised data/information.....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... of the computer system and network devices be carried out by: i. Internal team every six months and report is sent to CEO. ii. CERT-IN empanelled auditors preferably by STQC (Standardization, Testing & Quality Certification) under Department of Information Technology once every year. iii. Comply with the Cyber Security audit observations in time bound manner. 7.8 Guidelines for Computer Users or Operators: (a) DOs. (i) Observe effective physical security procedures to restrict access to computer systems. Access to be given only to authorized persons. (ii) Use hardware locks in the cabinets in which the computer system is housed. 136 (iii) The contents of cartridge tapes, CDs or Pen Drives are as good as written files. All physical and static protective measures and instructions laid down in this manual for document security will also apply to the use, control and custody of data CDs or Pen Drives. External storage media containing classified data will be marked and treated like other classified documents. (iv) All classified documents should be stored in an encrypted form in PCs as well as external storage devices. (v) Adopt effective physical access control procedures ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....CD(RW) and pen drives should be broken and destroyed and record to this effect should be maintained. (xx) All the used printer ribbons and carbons should be destroyed by burning. (xxi) Maintenance or rectification of faults in the computer system should be carried out under proper supervision. Keep an eye on the outside engineer attending to the fault in your computer system (xxii) Use UPS units to prevent corruption of data and software. (xxiii) Where feasible, all digital storage devices when permitted to be taken out, will be password protected and prior permission of security office is obtained. (xxiv) Some PCs have in-built physical locking system. The user should keep the computer locked when it is not in use and ensure safe custody of the operating and duplicate keys. (xxV) Culture of one printer or more per PC should be curbed. Ensure centralized printing within section. (xxvi) Network printers must be located in a secure place so that the documents being printed cannot be taken away by unauthorized personnel. (xxvii) Internet PC as well as patches released by OEM should be periodically updated. Live updates for Anti-virus/Anti-spyware and portable storage media use....
X X X X Extracts X X X X
X X X X Extracts X X X X
....CRET documents. It will be the responsibility of the authorized officer under whose supervision the PC work is being carried out. xi. Don't carry CDs outside the office building. In case a data stored media has to be taken outside the office building, its movement will be with prior approval. A record of the movement indicating full details like date or time of its being taken out, name of the officer taking it out and purpose, date and its time of its return etc will be maintained. Don't keep CDs in table drawers etc. xii. xiii. Don't become a member of unofficial chat club or official chat club on official Internet. XIV. Don't Carry Pornographic CDs or VCDs or such like material in other storage devices. XV. Do not use pen drives, internal CD writer or combo drives unless specially authorized. xvi. Do not use/install freely available screen saver on internet as these may have encoded spyware/Trojan. 7.9 Instructions for Use of Internet within Classified Area/Zone: Internet services are based on open architecture with minimal security features. They are also open to malicious attacks, hacking, virus activities and cyber-crimes. Unauthorized and unregulated use of internet ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....c. 7.9.3 Keeping in view the vulnerabilities involved in using internet in any sensitive / defence installation, apart from cyber security guidelines mentioned in the chapter, the following may be incorporated for security of the IT network(both internal & external) :- i. Instead of multiple internet connections, there should be limited internet gateways for accessing the internet from within the organisation. These limited internet connections must be closely monitored by the Information Security Operations Centre of the organization. ii. The SOC should include industry standard Security incident and Event Management (SIEM), Security Orchestration Automation and Response (SOAR) and User and Entity Behaviour Analytics (UEBA) solutions for faster response time during attacks and timely detection and blocking of attacks. 140 iii. All traffic through the organisational internet gateways must be screened to ensure that organizational data remains secure. Concerned personnel must be sensitized to the fact that their internet connections are provided to aid them in discharge of their duties and not for personal usage. iv. Communication through open e-mail should be avoided from dis....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... between the subcontractor and the ILDC shall be included in the contract with the following additional provisions: (a) Out sourcing partners personnel and facilities would also be covered under the Official Secrets Act, 1923, whenever the ILDC is handling classification material, document, information etc. (b) Persons working on such projects should be checked for character antecedents and police verification shall be obtained before inducting any person on such assignments. (c) All the relevant clauses of the Manual of Security are to be made applicable for the sub-contractor. 8.2 Terms and conditions related to classic information: Terms and conditions relating to retention, handling and destruction of classified information/material received or generated under the subcontract shall be clearly indicated in the main contract between the subcontractor and the prime ILDC. If certain classified information/material received or generated under the subcontract is intended to be retained, then the subcontractor has to comply with the provisions of this manual and give an undertaking of the same to ILDC and concerned Government agencies. 8.3 Engagement of consultants/advisers: IL....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... to be adopted. g) The Embarkation Firm / Agency will be responsible for enforcing the necessary security measures including provision of escort, if any, till the equipment is taken over by the receiving manufacturing Division / Unit or Factory. Where necessary, the consignee will detail an officer to go to the port of disembarkation to take over the Equipment. The receiving officer will cover the equipment or otherwise conceal it and, if necessary, unload and move it out of the port during night so that chances of leakage of information are minimized. Consignor's responsibility to arrange security vetted carrier/transport agency till the receipt by consignee needs to be included. h) Single point contact (Security Co-ordinator) shall be designated for controlled movement of classified materials and documents from foreign source with whom collaborators can communicate for secured transaction of TOT documents/Materials. 9.2 Warning to Consignees: 143 Consignors of classified equipment will warn Consignees of the classification of the Equipment and the precautions to be taken. Escorts will be detailed during movement of all classified equipment. Procedure followed for movement of....
X X X X Extracts X X X X
X X X X Extracts X X X X
....orted to Nodal Office after the visit within 24 hours through online portal of Vital Installation Information System (url: https://indianfrro.gov.in/viis/)preferably within two days but not later than fifteen days in any case. This will also be reported to /Nodal Office,in quarterly report. No foreigner shall be allowed to visit vital installation on the strength of tourist visa/e-tourist visa. b) For the duration of the visit, the foreign nationals will be escorted by the security officer or officer designated by the company. A log of all the escorts assigned to the Foreigner or an Indian representing a foreign company/nation shall be maintained by IILDCs for atleast till the next external security audit. c) No photography in the areas where work related to defence related projects will be permitted. It may also be ensured that viewing of contagious security areas does not occur. d) After the visit, the names and particulars of the foreign nationals, the purpose, duration and site of the visit are to be communicated to the Internal Agencies of Ministry of Home Affairs quarterly. Instructions received from Dept of Defence Productions, Ministry of Defence in this regard from time....
X X X X Extracts X X X X
X X X X Extracts X X X X
....ation. (b) If the visit to Manufacturing areas is considered necessary, the visitor should be allowed access to only these areas, which are relevant for the purpose of the visit. (c) Notwithstanding the above guidelines, no foreign visitor should be allowed to manufacturing and development areas of Electronics Warfare and secure communications. (d) The aforesaid guidelines should also apply to NRIs, Persons of Indian Origin, and Indian citizens representing foreign firms. 146 (e) No exposure as well as disclosure about activities undertaken at ILDC would be made to any foreign visitor without exclusive clearance from CEO/Head of ILDC. Such disclosures would be on minimum need basis. 10.2 Meetings: Meetings would mean conference, seminar, symposium, exhibit, convention, training course or such gathering. Meeting with foreigners pertaining to MoD projects / classified information is not permitted without the approval of MoD. 10.2.1 ILDCs may conduct meetings with regard to Government Projects, with limited number of people who are connected with the project. However, all concerned officials will be governed under OSA, 1923. The information which is to be disseminated shall be....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... of Vendors / Contractors and Casual Labourers: Security discipline needs to be imbibed among Vendors / Contractors and Casual Labourers for better efficiency of the overall Security system. This can be achieved by detailed briefing or small training capsule to contractors and on-the-job training to their casual labourers. A clause on termination of services / contract as the 148 case may be for breach of security of any kind must form part of the contract agreement between the ILDC and the Contractor/ Vendor. 11.6 Training of Project Work Trainees: ILDC's may permit trainees to undergo training / undertake project work, however, all such trainees shall not be employed in any classified projects nor have any access to classified areas/zones/offices. In addition, all the students must be properly briefed about the sensitivity of the organization and conduct expected from them on Information Security. Police Verification including Bonafide /Conduct certificates from respective college should accompany the sponsorship of Trainees before permitting the students / trainees to take up project work / training and proper identification badges to be issued to them. No trainee is permit....
X X X X Extracts X X X X
X X X X Extracts X X X X
.... the invitees where necessary and a security officer appointed to enforce security measures. 12.4 Rejects and Salvage: All Top Secret / Secret Equipment rejected during development, trial or manufacture will continue to bear its original security classification and receive appropriate security protection. If such equipment is no longer required, it will be dismantled and rendered unidentifiable. Such equipment will not be consigned to salvage unless it is downgraded to unclassified or shredded beyond recognition. All Hard disks pertaining to classified projects will, at no cost, be sent out for repair / recovery of data or salvage. Hard disks will always be removed before the CPU is sent to salvage. The hard disks will be destroyed under the supervision of Head of Security and certified to that effect. The disposal of non-sensitive scraps may be done M/s. MSTC. 150 12.5 Disaster Management: The ILDC shall draw elaborate disaster management plan to minimize loss of life and property with an aim to handle the situation with utmost promptness and efficiency to safe guard the plant from major catastrophic incidents like Earth Quake, Bomb Blast, Floods, Terrorist Attack, etc., The ....
X X X X Extracts X X X X
X X X X Extracts X X X X
....y audit of ILDC on an annual basis, to ascertain compliance of security instructions contained in this security manual. Apart from this, the MHA/MoD/respective 151 licensing authority shall be at liberty to visit any company which has been issued with a licence for private sector participation in defence under I(D&R) Act, 1951 & Arms Act, 1959, at its discretion, for a random security system assessment. 12.9 Penalty for Non-compliance of security guidelines by ILDC: 12.9.1 In the event of non-adherence of security guidelines by ILDC, action shall be taken against the ILDC and/or individual person(s) as per relevant Government regulations/provisions in various Acts, such as IPC, CrPC, I(D&R) Act, Arms Act, OSA, 1923 etc. The ILDCs are further liable for action against them in the event of any breach of security resulting into compromising national security and national interest under relevant provisions of Official Secrets Act, 1923. The penal action in case of violation of guidelines contained in this manual may also result in cancellation/suspension of Industrial License by the concerned licensing authority. In case of cancellation / suspension of industrial licence, completio....
X X X X Extracts X X X X
X X X X Extracts X X X X
....the necessary information upon request: 12.12 Retention of Classified Documents Generated Under IR&D Efforts: ILDCs may retain the classified documents that were generated in connection with their classified IR&D efforts for the duration of their facility is meeting the security manual requirements. Documents shall be clearly identified as "IR&D DOCUMENTS." ILDCs shall establish procedures for review of their IR&D documents on a recurring basis to reduce their classified inventory to the minimum. 12.13 Classified Waste Management: Classified waste shall be destroyed as soon as practicable. This applies to all waste material containing classified information. Pending destruction, classified waste shall be safeguarded as required for the level of classified material involved. Receptacles utilized to accumulate classified waste shall be clearly identified as containing classified material. 12.14 Waste Management: This shall include the scrap generated as well as the components rejected during the (Quality Assurance) QA evaluation, as individual the components may be useless but collectively and over time they could be assembled into a weapon. Comprehensive guidelines should be i....
X X X X Extracts X X X X
X X X X Extracts X X X X
....uthority 3Information of Production data/Sales dataQuarterly30th June 30th September 31st December 31st MarchNodal Office, DDP, concerned licensing authority 4Undertaking to MHA/MoD/DPIIT to comply with provisions of Security ManualImmediately and on half yearlyImmediately and on 30th September 31st MarchNodal Office, DDP, concerned licensing authority 5Self-certification on compliance to internal security Audit31st March31st MarchDDP, concerned licensing authority 6Annual Cyber Security Audit in case of classified information, if anyAnnually31st MarchMoD & Nodal Office, DDP 7Internal Inspection Reports of Manufacturing FacilitiesHalf yearly30" September and 31st MarchDDP 8Report on Loss/recovery/unearthed Arms & Ammunition and ExplosivesQuarterly30th June 30th September 31st December 31st MarchNodal Office, DDP, Local Police 155 9Report to /MHA/DDP on compliance with observations of Internal and External AuditQuarterly & within 15 days of visit30th June 30tl September 31st December 31st MarchNodal Office, DDP 10Report on Visit of foreign business visitorsImmediately and on Quarterly basisImmediately 30th June 30th September 31st December 31st MarchNodal Office, DDP, 11Action tak....
X X X X Extracts X X X X
X X X X Extracts X X X X
....Letters) (CEO/MD) * i. Each item under the issued license is to be mentioned. ii. Each successive report should also mention items mentioned in the previous form. 158 Annexure-III INFORMATION OF PRODUCTION DATA/SALES DATA Date- (i) Details of Industrial License : (ii) Period of reporting : (iii) Items for' which license granted : (iv) Status of commencement of : Commercial Production (v) Production data : S.No.ItemLicensed Quantity (if applicable)Quantity ProducedValueImport content (%) 1 2 3 4 (vi) Sale data: (please tick the appropriate box and furnish details of the entities) S.N o.ItemQuantityValue (in INR)Entity to whom sold Domestic (organisation)Export (countries) 1 2 3 4 (vii) Stock in hand/Balance Stock S.NoItemQuantity 1 2 3 4 Place : [Signature] Date: Name (Block Letters) (CEO/MD) 159 Annexure-IV No. To D(DIP) Section, Department of Defence Production, Ministry of Defence Subject: Self certification on compliance to Security Manual for Licensed Defence Indsutries In regard to Industrial License No I issued to M/s hereby declare that our company is complying with the provisions mentioned in the Security Manual for Licensed Defence I....
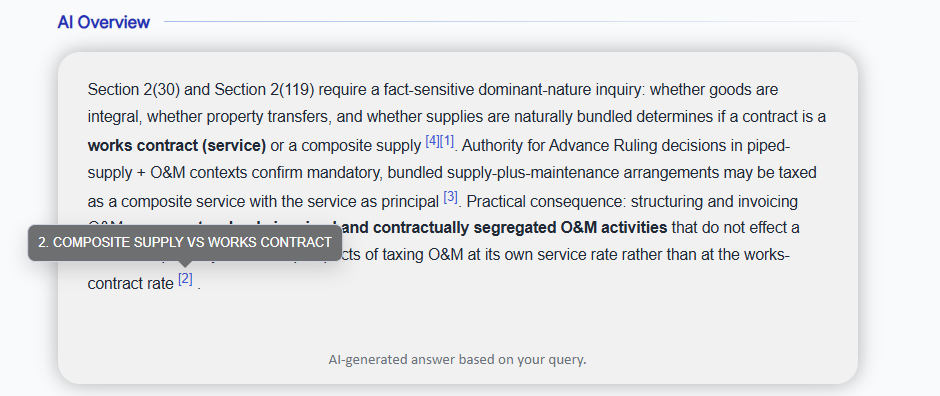
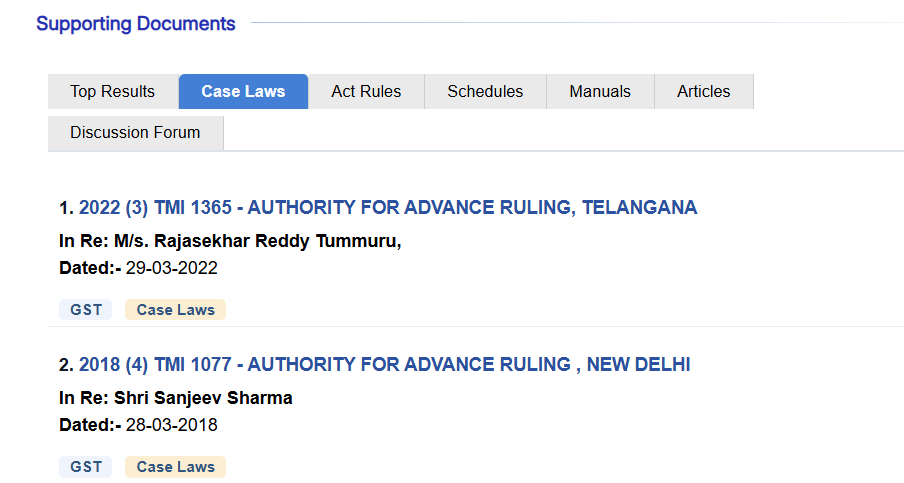
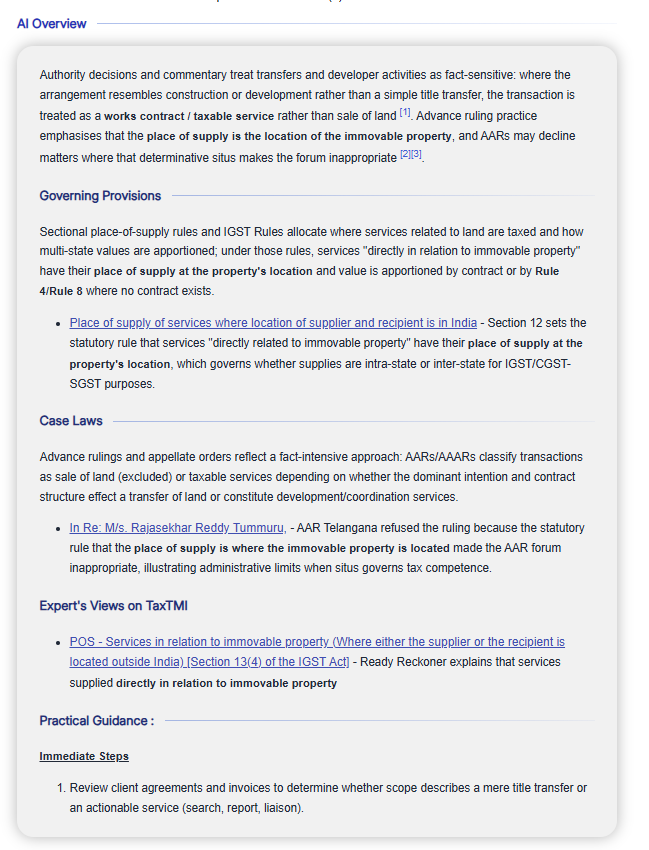
 TaxTMI
TaxTMI  TaxTMI
TaxTMI